FCC Proposes to Strengthen Cybersecurity of Emergency Alert Systems
Theo Wargo/Getty Images
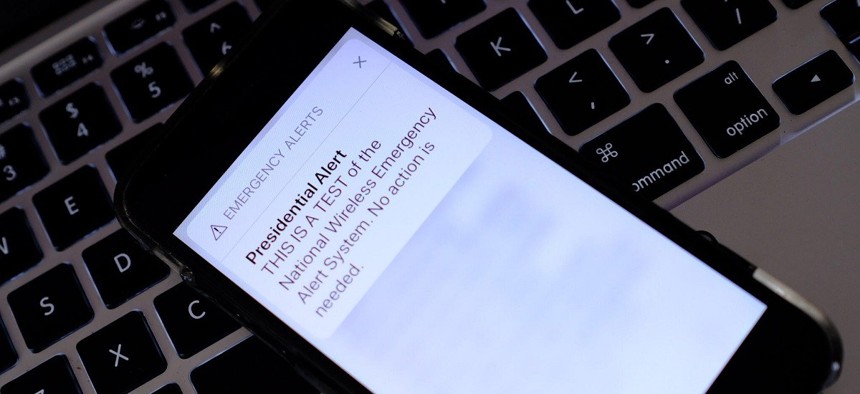
The notice of proposed rulemaking would require emergency alert system participants to disclose cyber breaches within 72 hours of discovery.
The Federal Communications Commission recently voted to approve a notice of proposed rulemaking that seeks to enhance the cybersecurity of the nation’s public warning system, by requiring, in part, that operators of the emergency alert system—or EAS—report any breaches of their equipment to the agency within 72 hours.
The proposal, which the FCC passed in a 4-0 vote on Oct. 27, would require that participants in the system “report any incident of unauthorized access of its EAS equipment” to the commission within three days of “when it knew or should have known that an incident has occurred.” EAS participants would be required to notify the agency within that timeframe and provide information concerning the breach, regardless of whether or not “that compromise has resulted in the transmission of a false alert.”
The EAS and wireless emergency alert—or WEA—systems are used to communicate emergency information to the public, often in response to severe weather, disasters or missing children. The alerts—which are issued by local, state and federal authorities—are delivered through radio broadcasts, television and mobile text messages.
“We believe the proposed rule is justified in light of the instances of false EAS alerts in recent years, caused by compromised EAS equipment being used to transmit a false message,” the FCC’s notice of proposed rulemaking said.
The vote came after the Federal Emergency Management Agency issued an advisory on Aug. 1 warning of “certain vulnerabilities in EAS encoder/decoder devices that, if not updated to most recent software versions, could allow an actor to issue EAS alerts over the host infrastructure (TV, radio, cable network).”
Previous incidents—both intentional and unintentional—have underscored the panic that can be caused by false emergency alerts. In January 2018, a Hawaii emergency management services employee mistakenly sent out an alert that warned residents to seek cover from an incoming ballistic missile. And in 2020, a local cable TV emergency alert system in Washington state was breached by a hacker, who sent out false warnings about a radiological emergency.
In addition to enhancing breach reporting requirements for EAS participants, the proposed rule would also require that EAS participants and commercial mobile service providers who are a part of the WEA system “annually certify to having a cybersecurity risk management plan in place and to employ sufficient security measures to ensure the confidentiality, integrity and availability of their respective alerting systems.”
In a statement, FCC Commissioner Geoffrey Starks cited data collected by the agency’s Public Safety and Homeland Security Bureau during a nationwide EAS test in August 2021, which found that “more than 5,000 EAS participants were using outdated software or using equipment that no longer supported regular software updates.”
Stark also praised the proposed rulemaking for seeking public comment on whether or not WEA participants should also be required to report to the FCC about unauthorized access to their systems and equipment.
“This is an important step,” Stark said. “Without notice, unauthorized access could continue unabetted and spread to other EAS and WEA systems.”
FCC Chairwoman Jessica Rosenworcel also said in a statement that the agency’s rulemaking was needed to help bolster the operational readiness of the nation’s public alert systems.
“This effort will help ensure the function of these essential systems in emergencies and that the public can trust the warnings they receive,” Rosenworcel said. “This is important because the Department of Homeland Security recently determined that some of this alerting infrastructure is susceptible to serious security vulnerabilities. While some patches have been released to fix these flaws, not everyone has installed them. We are committed to fixing that here and now.”
During an October event hosted by the Washington Post, Deputy National Security Advisor Anne Neuberger cited the FCC’s effort to reduce the risk of cyber threats to public warning systems as one component of the Biden administration’s efforts to shore up the digital security of the nation’s critical infrastructure sectors.
The FCC’s notice of proposed rulemaking is open for public comment 30 days from the rule’s announcement on Oct. 27, and a total of 60 days for reply comments. The agency will then vote on whether or not to adopt the rules.






