Back to the Future: Protecting Against Quantum Computing
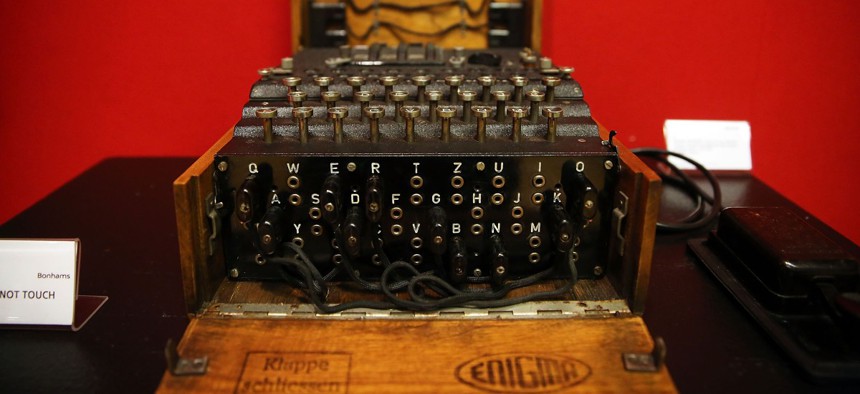
A working Enigma cipher machine that along with the 1942 56-page notebook belonging to codebreaker Alan Turing was auctioned Bonham's auction house on April 9, 2015 in New York City. Spencer Platt/Getty Images
Lessons from Germany’s World War II code machine, Enigma, show that even “unbreakable” encryption can be cracked eventually.
The previous two years have proven the importance of proactively working to secure our data, especially as organizations underwent digital transformations and suffered increased cyberattacks as a result. For those organizations that have been breached, but their data hasn’t yet been exploited and released to the wild, it may already be too late.
Organizations that have already experienced a data breach may become victims of “harvest today, decrypt tomorrow” or capture-now-decrypt-later attacks. These attacks, also referred to as “harvesting” for short, capitalize on known vulnerabilities to steal data that may not even be truly accessible using today’s decryption technologies.
These attacks require long-term planning and projections on the advancement of quantum-computing technologies. While these technologies may still be years away from being commercially available and widely used, organizations should look to protect against these threats now to prevent themselves from becoming a future casualty.
Before getting into more detail on the future threat posed by quantum computing, we should look to a historic example to inform our present decision-making.
Lessons from the Enigma
In 1919 a Dutchman invented an encoding machine that was universally adopted by the German army, called “the Enigma.” Unbeknownst to Germany, the Allied powers managed to break the coding scheme, and were able to decode some messages as early as 1939, when the first German boots set foot in Poland. For years, however, the German army believed the Enigma codes were unbreakable and was communicating in confidence, never realizing their messages were out in the open.
History may already be repeating itself. I can’t help but think that most organizations today also believe that their encrypted data is safe, but someone else may be close to, or already, reading their “secure” mail without them even knowing.
Today’s modern cryptography is often deemed unbreakable, but a big, shiny black building in Maryland suggests that governments may be better at this than is widely believed. Although a lot of credit goes to the magical and elusive quantum computer, the reality is different: poor implementations of crypto suites are the primary vector for breaking encryption of captured traffic. So are certificates captured through other means, brute-forced passwords and even brute-forced crypto, because insufficient entropy is used to generate random numbers.
All these techniques are part of the arsenal of any nation who wants to strategically collect information on the happenings of other international players—whether government or private companies. These techniques also require higher levels of coordination and financial backing to be a successful part of an intelligence strategy. As I continue to see, when the value of the captured information is high enough, the investment is worth it. Consider then the vast data centers being built by many governments: they are full of spinning disks of memory storage just in case current approaches don't yield access. Data storage has become an investment in the future of intelligence gathering.
Looking towards the future
Harvesting attacks does not just work as a strategy for quantum computers. We will likely have more powerful processors for brute-forcing in the future. Additionally, other types of stochastic computation machines, such as spintronics, are showing promise and even the de-quantification of popular algorithms may one day see a binary computer version of Peter Shor’s algorithm. The latter helps us explain how quantum computing may help to make quick work of current encryption techniques. This will allow breaking of Diffie-Hellman key exchanges or RSA on a conventional computer in smaller time frames.
So how do we shield ourselves? It is hard to imagine armoring oneself against any possible threat to encryption. Just like it is difficult to predict exactly which stocks will do well, and which ones won't. There are too many factors and too much chaos. One is left with only the option of diversification: using an out-of-band key distributing strategy that allows multiple paths for key and data to flow, and a range of algorithms and keys to be used. By diversifying our cryptographic approaches we are also able to minimize the damage in case a particular strategy fails us. Monocultures are at risk of pandemics, let's not fall victim to encryption monoculture as we move into the future.
It is past time to take steps now that will protect organizations from future threats. This includes developing actionable standards. Both federal agencies and the private sector need to embrace quantum-safe encryption. Additionally, they should look to develop next-generation, standards-based systems that will address current encryption method shortcomings and poor key management practices. This will help to ensure not only quantum-safe protection from future threats, but also stronger security from contemporary threats.
Organizations face a dizzying array of threats and need to constantly remain vigilant to thwart attacks. While looking to protect against current threats is certainly important, organizations should begin projecting future threats, including the threat posed by quantum computing. As technology continues to advance each day, one should remember that past encryption, like the Enigma machine, didn’t remain an enigma for long and was broken in time. The advent of quantum computing may soon make our “unbreakable” codes go the way of the dinosaur. Prepare accordingly.





