Encryption
Lawmakers question VPN impact on Americans' FISA surveillance protections
Democrats from both chambers sent a letter questioning the impacts to the Director of National Intelligence as Congress faces a deadline to renew FISA Section 702, which allows warrantless collection of foreigners’ communications overseas.
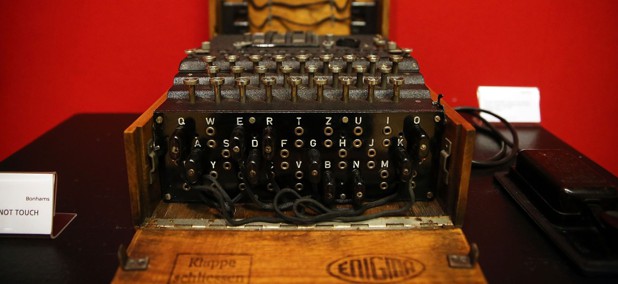
UK ‘agreed to drop’ backdoor encryption demand for Apple, DNI says
Director of National Intelligence Tulsi Gabbard said the United Kingdom has abandoned its effort to require that Apple provide its law enforcement and intelligence personnel with “blanket capability” to access customers’ encrypted files.
Cybersecurity matters: Preparing for the perfect storm
COMMENTARY | The best time to repair the roof is when the sun is shining, according to former Defense Department Chief Information Officer Terry Halvorsen.
Lawmakers warn that UK’s Apple backdoor demand ‘sets a dangerous precedent’
Rep. Jamie Raskin, D-Md., ranking member of the House Judiciary Committee, said "forcing companies to circumvent their own encrypted services in the name of security is the beginning of a dangerous slippery slope."
Signal clone used by Waltz to archive messages suspends services after reported hack
Smarsh, the Oregon-based owner of TeleMessage, said Monday it was “investigating a potential security incident” and suspended its services out of an abundance of caution.
Government interest in chat archiving service skyrockets following Signalgate
Top staffers across the government have reached out to Whiterock Technologies about its electronic communications preservation service amid a court ruling tied to last week’s Signal chat with top administration officials that accidentally included The Atlantic’s Jeffrey Goldberg.
US lawmakers ask UK court for transparency into Apple backdoor order
The court order issued by the United Kingdom centers on the UK’s 2016 Investigatory Powers Act, which was invoked to demand Apple provide a backdoor into users’ encrypted iCloud backups.
US spy chief directs legal review of UK’s Apple backdoor demand
Tulsi Gabbard called the order, which demands Apple permit the United Kingdom backdoor access into global users’ iCloud backups, a “clear and egregious” violation of Americans’ privacy.
Lawmaker looks to strengthen security of U.S. communications following UK’s Apple backdoor order
Sen. Ron Wyden, D-Ore., released a discussion draft of a measure to reform the CLOUD Act after the UK ordered Apple to build a backdoor into encrypted iCloud backups.
Lawmakers ask DNI to reassess UK cyber, intel ties over Apple backdoor mandate
The court order issued by the United Kingdom centers on the UK’s 2016 Investigatory Powers Act, which was reportedly invoked to demand Apple provide a backdoor into users’ encrypted iCloud backups.
NIST approves 14 new quantum encryption algorithms for standardization
Following the release of the first set of post-quantum encryption algorithms, the National Institute of Standards and Technology is advancing a second series of options to protect important data.
NIST will fire the ‘starting gun’ in the race to quantum encryption
Experts in the public and private sectors highlighted how to proactively transition networks to quantum-resilient standards.
NIST Releases Draft Post-Quantum Encryption Document
The agency continues its post-quantum cryptography push as it looks to create guidance for all sectors.
Featured eBooks