What Connected Patients Risk
Internet-enabled medical devices are designed to improve patient safety but pose a significant risk if left unsecured.
Patient care has evolved tremendously over the past three decades, including the reality that patients are increasingly connected from the moment of a medical incident to discharge and aftercare. Being connected allows for closer monitoring, automated delivery of medicine and rapid alerts, but do the benefits outweigh the risks if the devices aren’t secured?
Forescout researchers analyzed the Forescout Device Cloud, a repository of host and network information for more than 8 million unique devices to provide health care security and risk management leaders with insight into the types of devices connecting to networks and their associated risks. For this initial study, researchers limited Device Cloud analysis to 75 health care deployments with over 10,000 virtual local area networks and 1.5 million devices.
What are patients connected to anyway?
Blood glucose monitors, ingestible sensors and smart medical beds to assist with patient monitoring are just a few of the seemingly endless number of connected medical devices that patients may encounter. Every patient journey is different, but now patient needs dictate treatment and determine what they are connected to and how their data is shared. A patient requiring robotics surgery, for example, may be connected to significantly more devices than a patient being treated for a common cold.
Our research across 75 active deployments found that patient identification and tracking systems constituted the majority of devices (38%), followed by infusion pumps (32%) and patient monitors (12%).
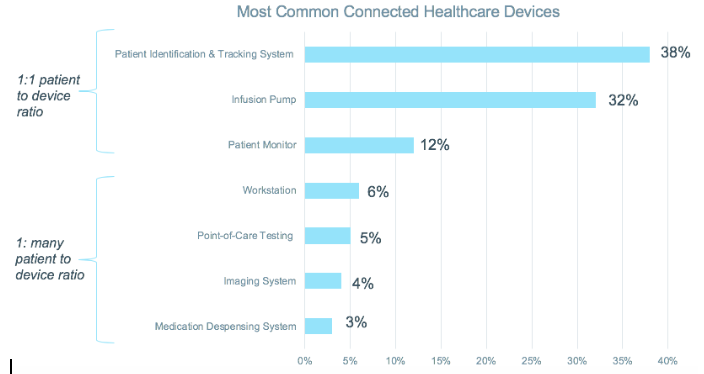
These top three devices are typically assigned to individual patients, reflecting a 1:1 patient to device ratio. The other commonly identified devices—workstations, point-of-care testing devices, imaging systems and medication dispensing systems—reflect a one-to-many patient to device ratio. What’s alarming about shared-use devices is that they are often long-lived devices—some of which have operated for more than a decade. Consequently, those devices may be running a 10-year-old operating system that might be unpatched—or worse, the OS may no longer be supported at all.
With the end of support for Windows 7 on the horizon, we investigated the number of devices running the Win7 OS and found that approximately 71% of devices will be left without support after January 2020; 0.4% were already running an unsupported OS; and only 29% were running a version of Windows that will be supported for more than a year.
It’s absolutely critical that health care security and risk management leaders realize the perils of an unsupported OS. With thousands of new vulnerabilities reported every year, running an unsupported OS would present a significant risk to health care organizations—and ultimately, patient safety.
Device Proliferation and the Convergence of IT, OT and IoT
With the internet of medical things, or IoMT, market expected to reach $136.8 billion worldwide by 2021, we wanted to understand the volume of actual medical devices on the network. We found that 53% of the connected devices were IT or traditional computing devices, such as personal computers, laptops, purpose-built workstations, servers, thick and thin clients, virtualization hypervisors and enterprise networking gear. We found that 8% were operational technology devices—a collection of connected medical devices and critical care systems as well as building automation/HVAC systems, power generators, badging and other facilities-related devices as well as IP-enabled security cameras and physical security systems. The rest—39%—were IoT devices that go beyond the IT and OT categories, including network printers, mobile devices, tablets, video conferencing devices, smart TVs and entertainment consoles.
These findings indicate that nearly half of the devices on medical networks are still non-traditional assets. There are simply more VoIP phones, connected printers, computer accessories and IoT gadgets than there are actual medical devices. Yet, each type of device presents a unique risk—and any device on the network can become an entry point for attack.
The IoMT Explosion is Changing the Role of the CISO
The health care industry prioritizes availability over confidentiality and integrity. Put simply, that means keeping the lights on and maintaining operations. Hospitals rely on a constant power supply for critical life support systems, and they have backup supplies and failover plans in the event of an emergency. What health care CISOs and other leaders must realize is that while the explosion of connected devices has resulted in countless benefits, the same devices now relied on to save a life, could become compromised and endanger the lives of patients. As our research revealed, health care networks are complex environments with thousands of connected devices and often, those networks aren’t segmented. And, when it comes to the actual devices, many of them are running an OS that will soon no longer be supported.
Connected medical devices are not inherently bad; however, the absence of medical device regulation has allowed manufacturers to rush their products to market, often with little or no security. The Food and Drug Administration has recognized the rapid growth of connected medical devices in recent years and has provided both pre- and postmarket guidance for the management of cybersecurity in medical devices. Although not legislation, the guidance clearly states that "medical device manufacturers and health care delivery organizations are responsible for putting appropriate mitigations in place to address patient safety risks and ensure proper device performance." However, just last year we saw that third-party vendors working with health care providers accounted for 20% of data breaches. There are multiple contributing factors, but ultimately there simply isn’t a workflow in place to manage the risks.
CISOs in the health care industry are facing a significant challenge. In addition to the proliferation of IoT and IoMT devices on health care networks, health care as a whole within the U.S. is shifting from a fee-for-service model to value-based payments, and mergers are becoming more common. With so many variables and so much change, security leaders must be flexible and open to change. They must lead the charge in the adoption of new connected devices, but they must also be the leaders in the communication of security risks. Many health care organizations and hospitals cite "improving the health of our patients and community" and "setting the standard of excellence in patient care" in their mission statements. The evolving role of the CISO is to not only ensure security and resiliency so that the mission can be fulfilled but to also communicate security risks effectively with fellow leaders and the organization as a whole.
Colby Proffitt is a cyber strategist at Forescout.






 By
By