Survey: Most Feds Who BYOD Do It Without Agency Approval

Georgejmclittle/Shutterstock.com
It’s hard for agency security officials to protect networks when they don’t know what’s connecting to them, experts say.
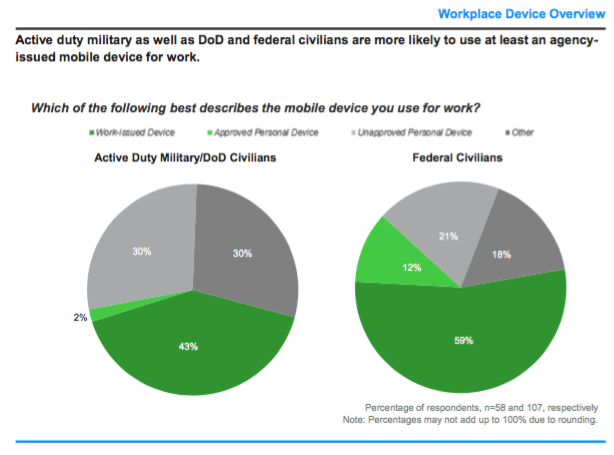
When federal and military employees are doing government work on mobile devices, those devices are usually agency-issued, but many who use personal devices say they aren’t getting agency approval.
That’s the upshot of a Government Business Council survey of 165 government employees on their use of mobile devices. GBC is the research arm of Nextgov publisher Government Executive Media Group.,
Among active duty military and Defense Department civilian employees, 43 percent said they use an agency-provided mobile device to conduct government work. On the civilian side, 59 percent said they use agency devices for work.
But about one-third of both groups said they do agency work on personal devices. Within those subsets, 94 percent of Defense employees said their personal devices have not been approved by the agency; 64 percent of civilian agency employees said the same.
Agencies have differing policies about employees bringing their own devices to work. Those policies largely exist to stem the vulnerabilities introduced by the use of unapproved devices. Personal devices are not necessarily less secure by their nature but federal security officials can’t know what additional steps may be necessary to protect the agency’s digital assets if they don’t know what devices are accessing them.
“Some of the basic tenets of network cybersecurity is to know who and what is riding on your network,” said Chris Cummiskey, former Homeland Security acting undersecretary and chief acquisition officer, now a senior fellow at George Washington University’s Center for Cyber and Homeland Security. “While ease of connecting personal devices to the network is convenient for employees, it poses a security challenge for IT professionals in identifying and blocking malicious activity that may exist at the endpoint.”
And survey respondents seem to be aware of the issues. Some 51 percent said security is more important than productivity—25 percent said the opposite. Similarly, 51 percent said their agency’s device policy introduces more security risk than is necessary.
“When you use a computer or smartphone for both work and personal activity, you have added significant risk your personal activity introduces malware that can access your business data and networks,” said Chuck Brooks, the first legislative director for Homeland Security’s Science and Technology Directorate, currently at General Dynamics Mission Systems serving as principal market growth strategist for cybersecurity and emerging technologies. “Many successful attacks aimed at both government and industry have come through phishing and spear-phishing that expanded into cross-contamination of device networks.”






