White House sounds alarm on threat from quantum computers
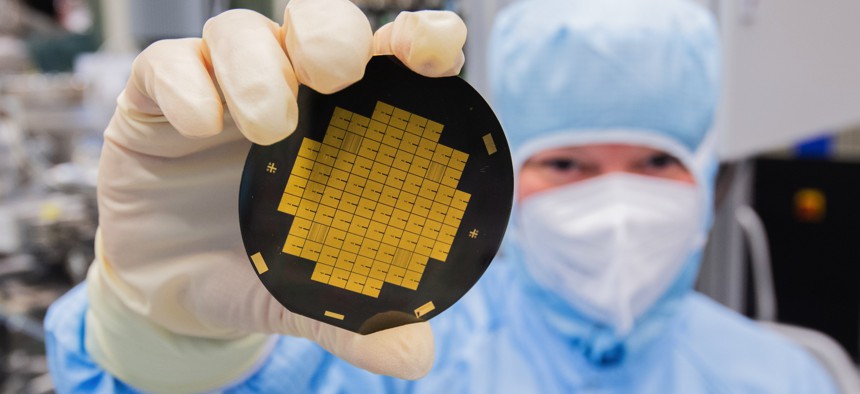
A research associate shows microchips for quantum processors in a clean room laboratory at the Physikalisch-Technische Bundesanstalt PTB in Braunschweig, Germany. Julian Stratenschulte/picture alliance via Getty Images
New directive orders the government to work with industry on security that can stand up to tomorrow’s quantum-powered decryption tools.
Hoping to move the world to better encryption before quantum-powered codebreaking tools arrive, the White House on Wednesday ordered federal agencies to ponder their security protocols and to jumpstart efforts to work with industry on new ones.
“Current research shows that at some point in the not-too-distant future, when quantum information science matures, quantum computers…will be capable of breaking much of the cryptography that currently secures our digital communication,” a senior White House official told reporters on Tuesday.
Much of the security encryption that operates in the background of digital life works essentially like combination locks. Just as you can open a combination lock if you have the patience to try all the possible combinations, so you can crack modern encryption if you have enough computing power and time—but in some cases, that means thousands of years.
Quantum computers, however, work fundamentally differently than conventional computers. Conventional computers rely on transistors, which form logic gates—basically little switches embedded on chip. In the same way a switch can take one of two positions, on or off, so conventional logic gates can produce one of two values, zero or one. String all of those zeros and ones together and you have modern computer code.
But at the quantum—that is, atomic—level, physics functions differently. It’s possible to create a unit of information called a quantum bit, or qubit, that doesn’t represent either zero or one but both at once. That promises to make quantum computing much faster than conventional computation—fast enough to open broad new possibilities artificial intelligence, breaking codes, and more.
Quantum computing is still in its infancy. Experts disagree on how to judge the performance of quantum versus regular computers. But there is wide consensus that quantum computers that can break extremely complex encryption will arrive at some point and probably this decade.
The new National Security Memorandum, or NSM, released by the White House on Wednesday requires federal agencies to bring their encryption up to standards.
“Given the complexity, costs, and time required to fully transition to quantum-resistant cryptographic standards, the NSM provides a roadmap for agencies to inventory their IT systems, with a requirement to set and meet specific milestones. Doing so will help ensure that Federal agencies get the support they need to fully and effectively protect their networks from future exploitation,” reads a fact sheet that the National Security Council released to reporters.
It also directs the National Institute of Standards and Technology to work with industry to “generate research on, and encourage widespread, equitable adoption of, quantum-resilient cryptographic standards and technologies.”
Needless to say, moving the world to a new set of cryptographic standards won’t be cheap. The White House officials said that that was why they wanted to start working with industry now so that private entities could help develop new encryption tools to withstand the dawn of quantum computing.
“Public-key cryptography that is used across the Internet is used obviously across the private sector as well. So if we move arm-in-arm to build out the new algorithms, build out new ways to share keys, that will also bring down the cost significantly and enable the sharing of the new processes and protocols that will need to be put in place to enable this, not only in the U.S., but… around the world as well,” said the official.
Fortunately, said another senior White House official, “You don't need the quantum computers to make one of these [new cryptographic standards]. You could design new classical algorithms that work on the routers and networks today that are resilient.”






