Bill to Let DHS Monitor Internet Traffic on Government Systems Advances
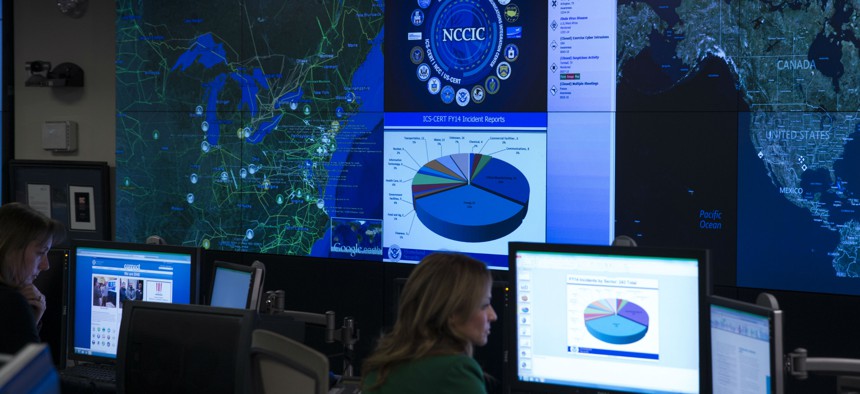
A view of the National Cybersecurity and Communications Integration Center before remarks by President Barack Obama, on Tuesday, Jan. 13, 2015, in Arlington, Va. Obama renewed his call for Congress to pass cybersecurity legislation, including a proposal t
The federal data security upgrade would the agency closer to the center of cybersecurity operations.
A Senate panel on Wednesday voted to set into law the Department of the Homeland Security's responsibility to monitor public Internet traffic on all government systems. The bill is designed to minimize the harm from breaches like those that hit the Office of Personnel Management.
The federal government was admittedly slow to scan OPM networks for signs of threats that ultimately manifested in the loss of confidential records on 21.5 million federal employees, national security personnel and their families. Even after the attack, only 45 percent of agencies are using DHS’s network-surveillance technology, according to lawmakers.
Under the new Federal Cybersecurity Enhancement Act of 2015, DHS would be allowed to override an agency's objections to using the tool, called EINSTEIN.
Within a year, DHS would have to deploy the technology "to detect cybersecurity risks in network traffic transiting or traveling to or from an agency information system," and to block that problematic Internet traffic, according to the bill.
During a meeting on Wednesday, the Homeland Security and Governmental Affairs Committee made a few changes to the legislation, including adding privacy protections. Then, without objection, members passed the proposal by a roll call vote. The bill was introduced on Monday by committee Chairman Sen. Ron Johnson, R-Wisc., and ranking Democrat Sen. Tom Carper, D-Del.
There now are more civil liberties clauses in the bill. Within six months after being signed into law, DHS would have to report to Congress on "privacy controls" for the intrusion prevention technology, according to the legislation. And the department must "periodically update" a privacy impact assessment of the surveillance technology, the legislation states.
One amendment would bake several privacy and transparency measures into EINSTEIN.
Another adjustment would require DHS to report any personal information caught by the monitoring system that has nothing to do with a threat. The department has said it plans to immediately purge any EINSTEIN records netted that do not trigger alarms. The tool sweeps up bulk traffic containing, among other things, emails and Web-surfing habits, including online banking sessions.
Some departments have questioned how EINSTEIN surveillance complies with legal restrictions against disclosing agency data. And privacy activists have been wary about widespread activation of the tool.
Is EINSTEIN Smart Enough?
The technology is informed by technical "indicators" of attacks that are discovered by the National Security Agency, as well as other government and industry organizations that study threats.
The legislation would require the government to tell Congress how successful EINSTEIN has been by reporting the number of times the tool thwarted threats and the types of indicators that were used to detect the dangers. Critics questioned the usefulness of the intelligence that has been fueling the system.
The new bill would make EINSTEIN try tactics other than indicator-detection as well as incorporate cutting-edge commercial technologies to improve success.
One provision unrelated to EINSTEIN would involve identifying all unclassified data on networks, that, when combined with other unclassified information, could produce a piece of classified intelligence. Another item would require a report to Congress on the damage to national security caused by the OPM data breaches.
Certain agency computer users would be obligated to sign in with a stronger form of identification. So-called multi-factor authentication -- which requires a password and something else like a smart card or text-message code -- is becoming standard for banking transactions and other online activities. Various toothless White House polices requiring smart card verification that date back to 2004 have not compelled agencies to upgrade system logins.
To the extent possible, criteria that measure an agency's security posture, such as "intrusion and incident detection and response times," would be published on a federal performance website. It took OPM until April to discover a breach that began around June 2014.
Agencies within a year would have to encrypt all mission-critical and sensitive data so that attackers cannot read any intercepted information.
In addition, the bill would make permanent a program begun in recent years called Continuous Diagnostics and Mitigation that provides agencies with sensors to improve visibility into their own networks.
The amended bill subsumes a similar Senate proposal introduced last week that would further empower Homeland Security.
According to a Senate aide, the whole package could be attached to a controversial House-passed cybersecurity bill that would exchange threat indicators -- including, sometimes, personal data -- between government and industry.
The committee’s provisions would expire in seven years.
"Had the powers of this bill been implemented already, they likely would have stopped the hack of the Office of Personnel Management," Johnson said in a statement upon introducing the bill. "They will make it far more difficult for our adversaries to steal our private data and to penetrate government networks."
NEXT STORY: CRS scrutinizes the OPM breach






