Einstein keeps an eye on agency networks
Voluntary network gateway monitoring program gives DHS a big-picture view of federal cybersecurity.
The Agriculture Department launched a cyberattack on another federal agency last summer, and no one knew about it — not even USDA.
The stealth attack occurred when a small number of USDA computers became infected with a computer worm. The malicious code began scanning network connections to find insecure computers it could build into a network, or botnet, of infected computers. The malicious code kept scanning until it reached the Transportation Department’s network gateway. Then it got caught.
DOT’s gateway was equipped with traffic sensors to detect computer worms and other malicious software. When the sensors detected unusual traffic, DOT’s monitoring system alerted the Homeland Security Department’s U.S. Computer Emergency Readiness Team. The alert and US-CERT’s response were swift because DOT participates in DHS’ voluntary Einstein program. DHS officials named the program Einstein because they think their monitoring program is smart.
Since 2004, Einstein has monitored participating agencies’ network gateways for traffic patterns that indicate the presence of computer worms or other unwanted traffic. By collecting traffic information summaries at agency gateways, Einstein gives US-CERT analysts and participating agencies a big-picture view of bad activity on federal networks.
US-CERT’s security analysts use Einstein data to correlate cross-agency security incidents. Participating agencies can go to a secure Web portal to view their own network gateway data.
Einstein doesn’t eliminate the need for intrusion-detection systems on agencies’ networks, said Mike Witt, deputy director of US-CERT. But the 24-hour monitoring program does give individual agencies a view of activity in other parts of the federal network infrastructure that could affect their own networks.
“Einstein is providing the first accurate and iterative picture of the health
of the federal government’s domain in real time,” Witt said.
Ten agencies participate in Einstein, and four or five others have indicated they plan to join by the end of the year. Witt said DHS officials hope to have most Cabinet-level agencies in the program by the end of 2008. DHS will try to expand participation to more of the midsize and small federal agencies later, he said.
“Einstein is not mandatory, so we have to do a sales job with agencies,” Witt said.
Witt wouldn’t name the agencies that have signed up. In a public presentation last year, however, a DHS official identified eight participants. They were DHS, DOT, the departments of State, Treasury and Education, the Federal Trade Commission, the Securities and Exchange Commission, and the U.S. Agency for International Development.
The Justice Department has since joined the program.
Vance Hitch, Justice’s chief information officer, said Einstein has made Justice networks more secure, but wider participation would improve security.
“The more data you get about who is being attacked and by whom, the better it is for all of us,” he said. “It is like connecting the dots.”
Participation in Einstein is voluntary, but a spokeswoman for the Office of Management and Budget said OMB strongly encourages participation in the program. She said Einstein is a good candidate for inclusion in OMB’s Security Line of Business, a governmentwide initiative to save money on systems and network security by consolidating agency spending.
DHS requested $13.9 million for the Einstein program in the fiscal 2008 business case documents it submitted to OMB. It requested an identical amount in 2007.
Agencies can participate in Einstein at no cost. DHS provides the hardware, software, support services and operational training that agencies need if they join the program.
US-CERT collects statistics that reflect a growing need for the capabilities Einstein offers. US-CERT received reports of 23,978 incidents in fiscal 2006, and more than 20,000 incidents have already been reported in fiscal 2007, said Jerry Dixon, director of DHS’ National Cyber Security Division, which operates US-CERT.
Each new worm or other type of malicious code reported to US-CERT is counted as a single incident, whether it affects 10 or 10,000 agency computers.
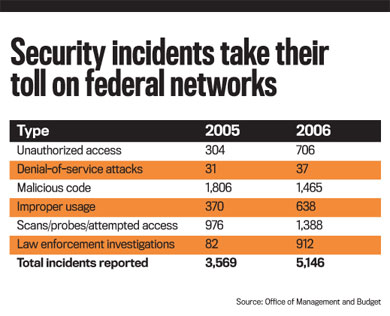
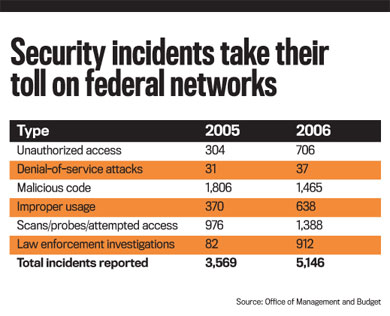
In its 2006 Federal Information Security Management Act report to Congress, OMB said the number of incidents all agencies reported to US-CERT grew 75 percent from the previous year. OMB attributed the spike to increased intrusions and a new executive order that requires agencies to inform US-CERT of all incidents involving the disclosure of personal identity information.
Federal statistics show that attacks on federal networks are growing more frequent and malicious. “Malware has gotten so pernicious [by] burrowing into the operating system so the attacker can control it in a hidden fashion,” said Ed Skodis, founder of Intelguardians, an information security consulting company, and author of a book on malware. The company works with federal law enforcement agencies and performs research for DHS.
Criminal hackers make money by using malicious code to gather information, and they use that money to develop sophisticated code that is harder to detect, Skodis said.
He said spear-phishing attacks get past agency firewalls and other defenses because they trick employees into clicking on links in official-looking e-mail messages that are fakes.
Employees’ PCs can — without the employees’ knowledge — become part of large botnets that attack other computers to steal information, money or both.
DHS’ Einstein uses a combination of commercial and government software to monitor botnets and other unauthorized code. Technicians install sensors outside an agency’s firewall to monitor incoming and outgoing Internet traffic, said Brent Wrisley, US-CERT’s director of situational awareness and technology.
“The only thing we need from the agency other than their cooperation is power to their system,” Wrisley said.
Once an Einstein setup is completed, the sensor components begin collecting traffic data. The output, which resembles a phone bill, is a log of all inbound and outbound traffic at an agency’s network gateway, US-CERT officials said.
“When we see strange activity, we will alert the computer incident response component of the agency, and they will investigate and report back to US-CERT,” Witt said.
Officials at Education, which participates in Einstein, said the program adds another layer of security that helps safeguard the agency’s critical networks and information systems.
“Einstein is like having more trip wires out there,” said Bill Vajda, Education’s CIO. “It is designed to help you make judgments and assessments in the context of the federal government.”
When Einstein sensors installed at DOT’s network gateway detected an intrusion attempt, technicians were able to trace the source to USDA.
USDA technicians then identified the infected computers by their IP addresses, disconnected them from the network and disinfected them, said Lynn Allen, the agency’s chief information security officer.
US-CERT officials said Einstein reduces from four or five days to four or five hours the time between a security incident and when they receive a report of it. USDA, DOT and US-CERT responded to the USDA incident in a matter of hours. That improved response time is one of the reasons federal security is moving in the right direction, security experts say.
“Einstein already has proven its value,” said Alan Paller, director of research at the SANS Institute, which offers training for systems and network administrators. “It is easily the best technology thing the government has done.”
Traffic analysis
Spear-phishing attacks
Fast incident response
OMB report to Congress on the Federal Information Security Management Act implementation (.pdf)
Traffic analysis
Spear-phishing attacks
Fast incident response
NEXT STORY: Education wants out of IT management business





