Hackers Mortify Drunk Drivers, Attack Syrian Electronic Army, and Pay Back MIT
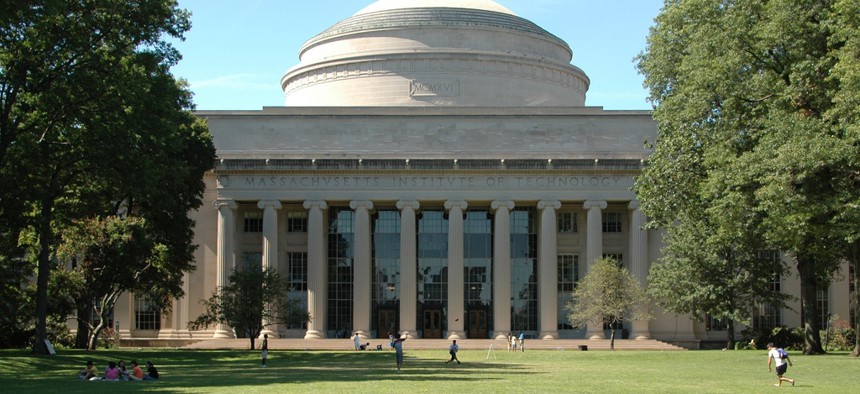
Flickr user rwhiddon
Just another week in ThreatWatch, our regularly updated index of noteworthy data breaches.
In case you missed our coverage this week in ThreatWatch, Nextgov’s
Cops name and shame drunk drivers on Twitter
Staffordshire Police are being investigated for potentially violating data protection laws by tweeting the identities of suspects, as part of a public awareness campaign.
Syrian Electronic Army gets taste of own medicine
The pro-regime hacktivist collective has discovered what it feels like to be a victim – after its own website was hacked by a rival group of Turkish attackers.
Neiman Marcus in-store shoppers at risk of financial fraud
The high-end retailer confirms it is investigating a cyber incident that exposed an unknown number of client payment cards.
MIT research site hacked in memory of information freedom legend
Anonymous targeted an entity that it partly blames for the suicide exactly one year ago of Aaron Swartz, co-founder of Reddit, Creative Commons and Demand Progress.
ThreatWatch is a regularly updated catalog of data breaches successfully striking every sector of the globe, as reported by journalists, researchers and the victims themselves.
NEXT STORY: Obama trims intelligence gathering






