Army eyes e-textbooks for ROTC courses
Officials look to develop multimedia digital library that is compatible with any type of e-reader.
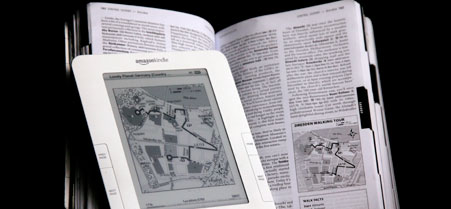 Richard Drew/AP
Richard Drew/AP
The Army is considering an ambitious project to convert its college-level Reserve Officer Training Corps textbooks to e-books that can take advantage of the multimedia capabilities offered by a digital library.
The Army Mission and Installation Contracting Command kicked off market research in late December, with an eye toward developing hardware-agnostic e-textbooks for the Army Cadet Command, headquartered at Fort Knox, Ky.
According to Daniel Elkins, a spokesman for the command's contracting office, the project covers textbooks that range from 217 to 511 pages. Topics include Army values and ethics, tactics and techniques, personal development, and leadership, he said.
"The concept is to take advantage of electronic media across all platforms, which would include content already in existing texts along with other media, such as embedded, video to further enhance learning," Elkins said in an email.
The market research notice said the Army wants to develop e-textbooks that run on Windows, Apple, and UNIX-based operating systems and are compatible with Kindle, Nook and Sony e-readers. The Army also wants to make e-textbooks readable on iPhone, iPad, Android and BlackBerry devices.
Army Cadet Command spokesman Mike Johnson said the intention is to develop e-textbooks across a range of platforms "so as to not pigeonhole the student into a particular device -- whether it is owned by the students or supplied by the college."
If the Army goes ahead with the project, students at 273 colleges that host ROTC programs would use them, Johnson said.
The service started laying the groundwork shortly after Daytona State College in Florida reported in the December issue of Educause Quarterly that students found e-textbooks less satisfying and more fatiguing than paper text in a two-year study financed by the Education Department. Professors surveyed in the study reported that students used e-textbooks less than paper text. "Many students did not do the required reading; they simply found it inconvenient," one instructor said.
The Army will base its procurement strategy on e-textbook market research. Industry responses are due Monday.
NEXT STORY: Data Unleashed Against Cancer






