Clinton Spokesman Quits Over WikiLeaks Comments
A State Department spokesman quit Sunday after he made disparaging remarks at a new media conference about the Defense Department's treatment of WikiLeaks' suspect Bradley Manning, revealing internal tensions that the Obama Administration faces in dealing with the technological forces changing the political landscape.
Manning, an Army private, has been charged with 34 offenses related to leaking more than 250,000 State Department cables and classified war logs from Iraq and Afghanistan.
"There is sometimes a need for secrets... for diplomatic progress to be made," Philip Crowley said in an off-the-cuff remark at the MIT conference, but added that the Defense Department's treatment of Manning was "ridiculous and counterproductive and stupid."
Manning was being held in solitary confinement at the Marine Corps brig in Quantico, V.A., where he was made to sleep naked to prevent him from harming himself, according to the Marine Corps.
Manning's pre-trial treatment, described in a letter by his attorney as "punitive" and "unlawful," has roiled human rights activists and prompted the United Nations to open an investigation into the conditions of his detention last December.
"The exercise of power in today's challenging times and relentless media environment must be prudent and consistent with our laws and values," said Crowley, in a statement released by the State Department on March 13 . He took full responsibility for his earlier remarks.
His remarks were intended to highlight the fact that any discreet actions taken by national security agencies had an impact on the country's global standing.
"It is with regret that I have accepted the resignation," Secretary of State Hillary Clinton said in a statement released in conjunction with Crowley's. She commended him for a "deep devotion to public policy and public diplomacy."
Principal Deputy Assistant Secretary Michael Hammer will serve as acting assistant secretary for public affairs.
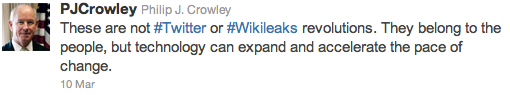
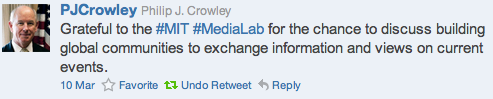
After the conference, Crowley tweeted on March 10,
NEXT STORY: The best of the federal blogosphere





