Energy Races to Build Quantum Encryption – for Citizens
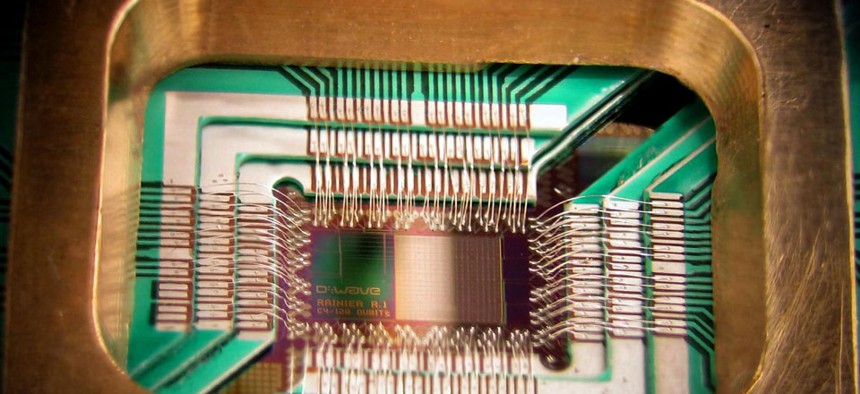
D-Wave Systems, Inc.'s DWave 128chip for quantum computing. Wikimedia Commons
At the same time, NSA and nation states race to crack conventional secret codes with quantum computers.
The Energy Department's Los Alamos National Laboratory and a Boston startup are joining efforts in a marathon to build uncrackable encryption for citizens who are increasingly concerned about snoops and government eavesdropping.
Supercomputers are expected to be able to break today's encryption formulas, as they grow exponentially faster. Foreign adversaries are believed to be at work on such “quantum computers” for that very purpose. Meanwhile, technology outfits -- and some federal agencies -- are countering the threat with "quantum encryption."
The deal between Los Alamos and Allied Minds subsidiary Whitewood Encryption Systems marks the lab's largest transfer of intellectual property.
"The company has licensed more than 21 separate pieces of intellectual property, making it the largest single licensing of its type" in Los Alamos' history, Energy spokesman James E. Rickman said in an email. The exact dollar amounts are proprietary, but will amount to a certain percentage of profits made by the Boston-based company.
Their tools have been under development for 20 years, according to officials at Los Alamos, a national security lab.
Quantum computers will be able to unravel algorithms at lightning speed, but quantum encryption can create cryptographic "keys" with lightning speed, backers say. The technique relies on physics, using unique particles of light -- called photons -- to physically move secret messages between two individuals. Today's encryption uses random-number generation based on mathematical formulas to make and break codes.
Any attempt to intercept messages secured with quantum encryption is detected because eavesdropping alters the properties of the key.
"If nobody tries to cut that letter open, it stays intact. If anybody tries to cut the envelope, what quantum physics tells us is, they'll actually change the information, so they'll destroy that information," said Matthew Green, a cryptography researcher at the Johns Hopkins Information Security Institute.
Los Alamos' designs are tailored to the needs of ordinary Americans and businesses. Lab officials claim the equipment can be as small as a computer thumb drive and could be produced very inexpensively to sell on the shelves of a consumer electronics store.
"If implemented on a wide scale," the technology "could ensure truly secure commerce, banking, communications and data transfer," officials said in a statement.
One drawback to quantum encryption is the amount and type of infrastructure involved. It requires running dedicated fiber optic cables between correspondents, potentially across continents and oceans. "The problem is that it's a real hassle to use," Green said.
This is not the government's first foray into quantum encryption. Energy awarded Qubitekk $3 million to create tamper-proof coding to fend off power grid cyberattacks, the San Diego firm announced last week. Under that arrangement, Qubitekk will be collaborating with several other U.S. national laboratories and Pacific Gas & Electric.
Meanwhile, other parts of the government are working on the opposite side of the crypto equation. There is speculation that the National Security Agency is making steady progress on “a cryptologically useful quantum computer" for code breaking, according to The Washington Post.
Most estimates on how close any organization is to truly achieving such a machine are at least a decade out.
As for Energy's code-making endeavor, Green said, "If the government's helping make things more secure, then that's good for everybody."






