Cyber Monday crackdown hits 132 websites
ICE
Immigration and Customs Enforcement targets alleged counterfeiters of trademarked goods.
In an operation that has become an annual rite of the holiday shopping season, law-enforcement agencies in the U.S. and Europe seized the domain names of 132 websites that were allegedly dealing in counterfeit versions of trademarked goods. For the third year running, U.S. Immigrations and Customs Enforcement announced the results of its crackdown on Cyber Monday, the busiest online shopping day of the year.
This year marked the first time that ICE collaborated with European enforcement agencies on the Cyber Monday operation. Non-U.S. sites included operations with top-level domain-name codes associated with Belgium, Denmark, the European Union, France, Romania, and the United Kingdom.
(FULL LIST: 101 U.S. Websites Blocked)
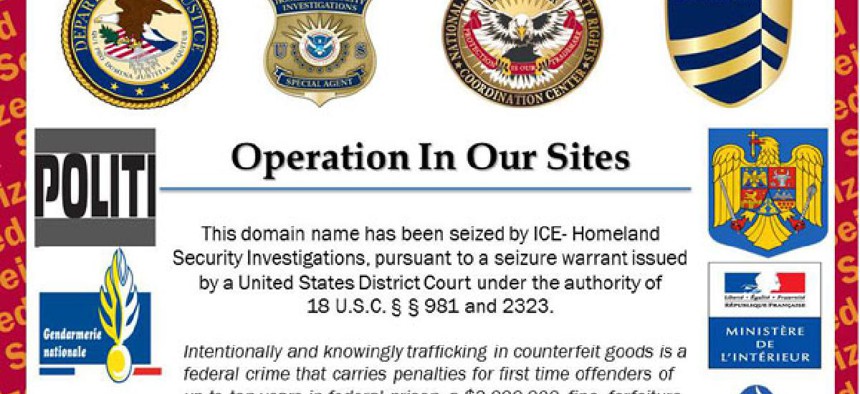
Websites are seized under the authority of a warrant issued by a judge. The content is deleted from the site, and replaced with an image announcing the seizure. The program has tallied 1,630 seizures since launching in 2010, and the In Our Sites banner has been viewed more than 110 million times.
From a practical standpoint, the operators of the sites can repost their storefronts to new domains in short order. Only one arrest was reported in the operation. Authorities are looking to seize about $175,000 from PayPal accounts linked to sales of counterfeit goods, but this amount is a drop in the bucket compared to the billions of dollars generated by such sales. The goods themselves are manufactured overseas, often in Asia, and are out of the reach of U.S. law enforcement.
To critics of the program, the seizure mechanism is especially unfair to legitimate merchants and site operators who are caught up in the sweep of Operation In Our Sites. Corynne McSherry of the Electronic Frontier Foundation says that while trademark pirates have no problem moving their operations to new domains, merchants who are trying to build up a customer base take a hit to their reputation and their online traffic when their sites are classified as illegal. McSherry cites the case of Spanish sports streaming site Rojadirecta, which was deemed legal in its home country, had its U.S. domains Rojadirecta.com and Rojadirecta.org seized in February 2011 and returned in August 2012. “The people that are really harmed are the people that shouldn’t be harmed—people that are engaging in lawful activity,” she said.
She also worries that the targets of In Our Sites are cherry-picked by industry, and aren’t properly investigated by law enforcement. “I think this is an effort to cast trademark enforcement in the light of consumer protection,” she said. “It doesn’t seem to me that this is the best use of our tax dollars—to protect the world from counterfeit Louis Vuitton handbags.”
This August, three members of Congress who are active on technology issues complained to Attorney General Eric Holder and Homeland Security Secretary Janet Napolitano about what they called insufficient due process and a lack of transparency under the program. In their letter, Reps. Zoe Lofgren, D-Calif., Jason Chaffetz, R-Utah, and Jared Polis, D-Colo., addressed the case of the music blog Dajaz1, which was taken down in 2010 during the first In Our Sites effort, and which remained closed for more than a year before the government quietly dropped its copyright infringement case against its operator.
Lofgren is looking to Web users for help drafting new legislation that would establish a procedure for appealing domain seizures. She posted her request on the popular online community Reddit last week.
The experience with Dajaz1 may have led to a shift in the targets of the program, which this year focused exclusively on physical goods shipped from merchants to customers, rather than digital products conveyed via download. Much of the case against Dajaz1 was focused on links to allegedly pirated content, which turned out to have been supplied by record labels. The 2012 Operation In Our Sites crackdown focused on counterfeit goods like name-brand handbags, DVDs, athletic gear, sunglasses, caps, sneakers, and even a popular European brand of baby carriers. “This is a purchase that expectant parents shouldn’t have to worry about,” said ICE Director John Morton in a conference call announcing the results of the operation.






