sponsor content What's this?
SMS-Delivered Tokens May Go Away in Multifactor Authentication, but Agencies Have Numerous Other Options
Presented by
FedTech

The National Institute of Standards and Technology recommends agencies phase out the use of SMS-delivered passwords in two-factor authentication.
The days of federal agency employees using a one-time password delivered via SMS text messages may be numbered, at least as far as the National Institute of Standards and Technology (NIST) is concerned. However, agencies will still have several different ways to enable multifactor authentication technology to secure their IT systems and networks.
In late July, NIST updated its special publication 800-63-3, its Digital Authentication Guideline, recommending that agencies move away from SMS as a method for users to receive a second authentication factor.
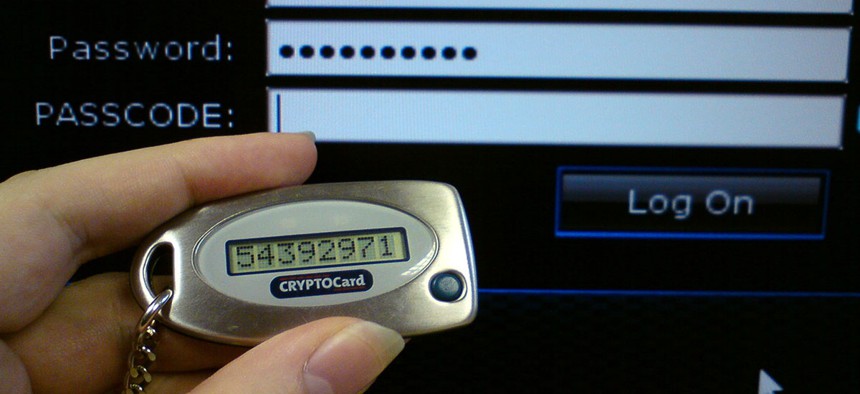
As the NIST report notes, there are three factors that serve as the cornerstones of authentication: something users know (for example, a password); something users have (such as an ID badge or a cryptographic key); and something users are (for example, a fingerprint or other biometric data). Multifactor authentication refers to the use of more than one of the factors, and the strength of authentication systems is largely based on the number of factors incorporated by the system.
Phasing out SMS as a Second Factor
Paul Grassi, NIST’s senior standards and technology adviser, laid out the rationale for NIST’s draft decision (which is open for public comment on the agency’s GitHub page until Sept. 17), in a blog post.
While tying authentication to a physical device can help improve security, thanks to the proliferation of Voice over IP applications and internet-based chat apps, it’s not clear that all SMS messages are going to physical mobile devices.
“It’s a beautiful thing about SMS interoperability that we can send a message to a ‘phone number’ without really caring if it’s an SMS, MMS, iMessage, or data message to some other internet service,” Grassi wrote. “An SMS sent from a mobile phone might seamlessly switch to an internet message delivered to, say, a Skype or Google Voice phone number. Users shouldn’t have to know the difference when they hit send — that’s part of the internet’s magic.”
However, that poses a problem for security, Grassi wrote. “That’s why we’re proposing that federal agencies first verify that the phone number is truly attached to a mobile phone,” he wrote. “If not (and the user happens to protect her or his VoIP account with a password), the user might now be protecting sensitive personal information with two passwords — that’s two of one factor type (two of ‘something you know’) rather than actual two factor authentication (‘something you know’ and ‘something you have’). So we felt we had to propose ruling VoIP out.”
In cases where NIST is confident that SMS messages are really going to mobile devices, Grassi notes that it is becoming easier for hackers to successfully redirect or intercept SMS messages on a large scale.
“While a password coupled with SMS has a much higher level of protection relative to passwords alone, it doesn’t have the strength of device authentication mechanisms inherent in the other authenticators allowable in NIST draft SP 800-63-3,” he wrote. “It’s not just the vulnerability of someone stealing your phone. It’s about the SMS that’s sent to the user being read by a malicious actor without getting her or his grubby paws on your phone.”
As a result, NIST is discouraging the use of SMS as a method for delivering a one-time code for multifactor authentication, and is recommending that the use of SMS as a second factor be reconsidered in future agency authentication systems. Instead of recommending that agencies remove the use of SMS in multifactor authentication systems, which would not be practical overnight, NIST is signaling that SMS is on its way out. “It’s up to agencies to make the risk-based decisions that best serve their constituents today and future-proof systems for tomorrow,” Grassi writes.
Other Multifactor Authentication Options
The good news for agencies and their employees is that there are several other methods for enabling multifactor authentication.
NIST notes that “authentication systems that incorporate all three factors offer better security than systems that only incorporate two of the factors.”
Many modern smartphones, including Apple’s iPhone and phones running Google’s Android operating system, can run applications that generate random, one-time authentication keys or passwords to serve as a second factor (along with a password known only to the user).
Additionally, as FedScoop reported, Jeremy Grant, the former head of the Obama administration’s National Strategy for Trusted Identities in Cyberspace, wrote a blog post about another method. Grant is an advisor to the FIDO Alliance, a nonprofit focused on developing technical specifications that define an open and interoperable set of mechanisms aimed at reducing the reliance on passwords to authenticate users. Grant notes that most mobile devices and computers are shipping with a secure, embedded hardware component — it can’t be hacked — separated from the rest of the device. Those hardware components, including Microsoft’s Trusted Platform Module, Apple’s Secure Enclave or Android’s Trusted Execution Environment, can be used to store a private encryption key.
NIST notes that biometrics such as fingerprints and iris scans, “when employed as a single factor of authentication, do not constitute acceptable secrets for digital authentication, but they do have their place in this specification.”
“For example, consider a piece of hardware (the authenticator) that contains a cryptographic key (the authenticator secret) where access is protected with a fingerprint,” NIST notes. “When used with the biometric, the cryptographic key produces an output that is used in the authentication process to authenticate the claimant. An impostor must steal the encrypted key (by stealing the hardware) and replicate the fingerprint to use the authenticator.”
For more on how the federal government is thinking about multifactor authentication, visit fedtechmagazine.com/multifactor.
This content is made possible by FedTech. The editorial staff of Nextgov was not involved in its preparation.





