Analysis: Go Ahead, Mess With Texas Instruments
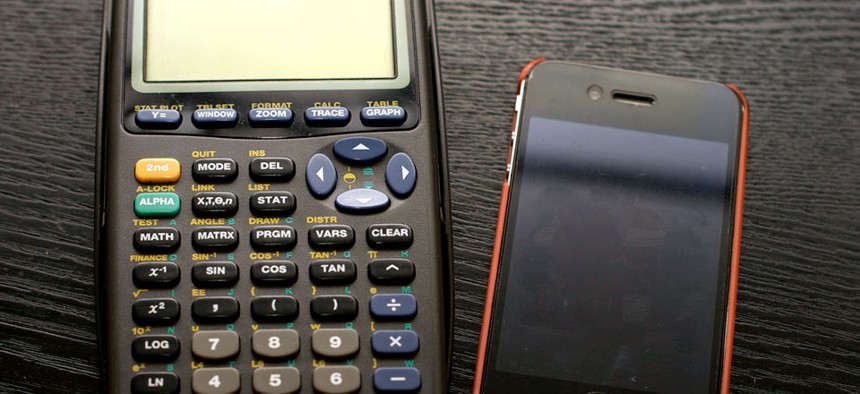
The TI-83 calculator matched up with an iPhone Flickr user JenGallardo
Why educational technologies should be more like graphing calculators and less like iPads. An Object Lesson.
Last year, while cleaning out the basement of my childhood home, I discovered a plastic storage bin marked "Calcusoft." Inside were piles of notebooks filled with sketches, storyboards, and lines of code, and buried beneath it all, a TI-83 Plus graphing calculator.
I bought the calculator the summer before eighth grade, when it was included on a list of required supplies for students entering algebra. At the time, owning a graphing calculator was a small but significant rite of passage for a junior high student. It was a sign of academic sophistication. It announced to younger peers that the equations you were expected to solve outpaced the primitive features of meager, four-function devices. But most importantly, graphing calculators were programmable, which meant they were equipped to play games. While possession of a traditional handheld gaming system constituted a brazen breach of school rules, playing games on a calculator maintained the appearance of genuine scholarly work. A graphing calculator was like having a school-sanctioned Game Boy.
Calculators did not always have this allure. The earliest handheld models were only "programmable" in the sense that they used rudimentary code to complete repetitive computational tasks more efficiently. It wasn't until 1990, when Texas Instruments released the TI-81 graphing calculator, that the medium became a feasible platform for game design. Unlike earlier devices, the TI-81 was equipped with a simple yet versatile programming language called TI-BASIC. Anyone willing to learn a few elementary commands could create text, graphics, and movement in minutes.
A decade had passed by the time I purchased my graphing calculator, and in the years between a robust online community had formed. These programmers -- many of them high school students -- had even figured out how to program their calculators in more complex source languages. Unfortunately, accessing such games required specialized knowledge and equipment, making the best programs precious. I wanted more of these high-quality games, and I wanted to learn how to make them.





