The Databases That Facial-Recognition Apps Need to Survive
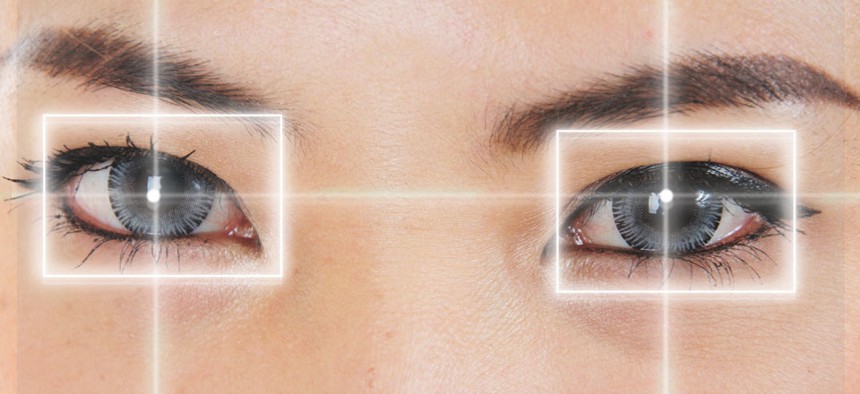
Keepsmiling4u/Shutterstock.com
Ensuring legal and social pressure demands responsible behavior.
Privacy concerns have been ignited by “NameTag,” a facial-recognition app designed to reveal personal information after analyzing photos taken on mobile devices. Many are concerned thatGoogle Glass will abandon its prohibition on facial recognition apps. And, there are open questions about the proper protocols for opting customers in and out of services that identify people through facial comparisons in real time. These kinds of services are technically "face matching" services, though they are colloquially referred to here as "facial-recognition technologies."
Ultimately, the coming wave of consumer facial-recognition technologies brings bad and good news. The bad news is obvious: Automatically identifying one of our most unique and personal traits raises serious privacy concerns ranging from stalking to loss of obscurity in public.
The good news is that facial-recognition technology—at least the kind that could be used at scale to identify most people in any given place—has an Achilles heel that buys society enough time to respond appropriately. No matter how powerful a facial-recognition app is designed to be, it can’t get the job done without being connected to a database that links names to faces, such as those owned by Facebook or LinkedIn. Going forward the key is to ensure legal and social pressure demands the same responsible behavior from database owners as it does from designers, hosts, and users of facial-recognition technologies.
Read the full story at TheAtlanticCities.com.
(Image via Keepsmiling4u/Shutterstock.com)





