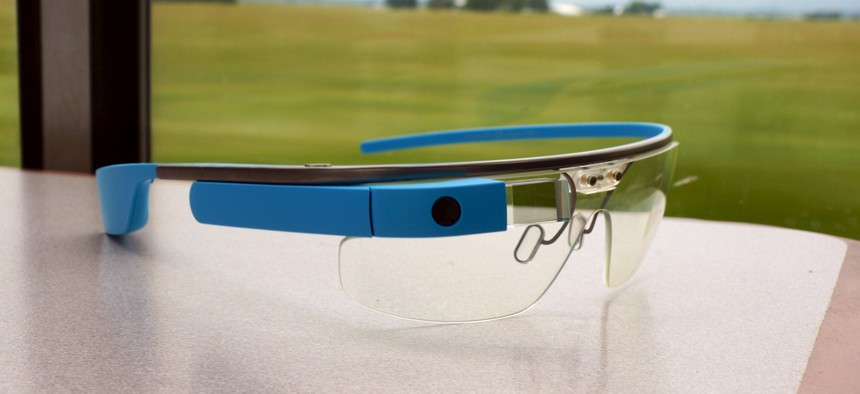
The Real Plan for Google Glass May Be To Sell It to Businesses, Not Consumers
Flickr user tedeytan
The indications are that the main customers for new tech may be big businesses.
Yesterday evening in New York City, Google’s Glass team threw a party. It brought together “Explorers” and “Influencers”—the lucky few people who got to try out the computerized glasses Google is developing. Over cocktails and hors d’oeuvres, the diverse crowd gushed about the joys and dissected the drawbacks of the device, which they’ve been wearing for the last few months.
The takeaway? Google Glass is not for who you think it is. Though Google has been promoting the device with heart-warming videos on rollercoaster rides and in children’s playgrounds, for the next few years at least, its main customers will be large businesses.
Members of the Glass operations team have been on the road showing it off to companies and organizations, and they told Quartz that some of the most enthusiastic responses have come from manufacturers, teachers, medical companies, and hospitals. That suggests that they may be trying to persuade firms to buy the device and develop applications for it.
Read the full story at Quartz.
(Image via Flickr user tedeytan )
NEXT STORY: The Bitcoin of Governance Could Be Coming Soon





