NASA's Newest Space Telescope Sends Back Its First Images of the Sun, and They're Gorgeous
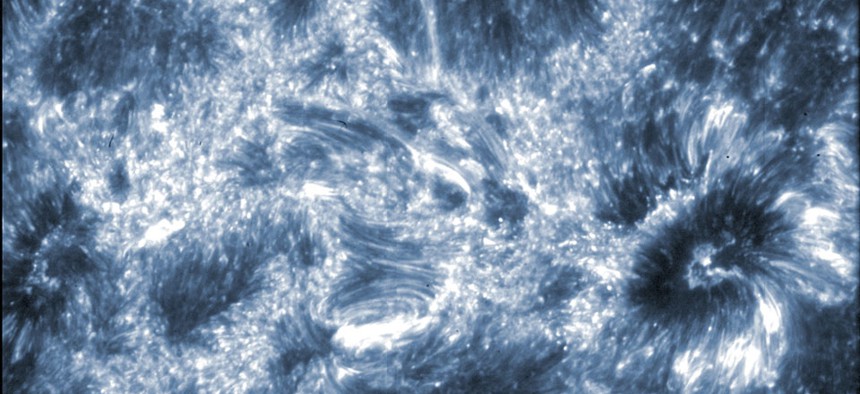
An image of the sun taken by the ISIS telescope Harvard-Smithsonian Center for Astrophysics/NASA
Early evidence suggests that IRIS is going to be a feast for those who love pretty pictures of space.
Last month, NASA launched a new telescope, known as IRIS, into space to study the sun. Today we got our first glimpse of what IRIS is seeing, and ... wow.
Even NASA's press release bubbled with excitement:
The moment when a telescope first opens its doors represents the culmination of years of work and planning -- while simultaneously laying the groundwork for a wealth of research and answers yet to come. It is a moment of excitement and perhaps even a little uncertainty. On July 17, 2013, the international team of scientists and engineers who supported and built NASA's Interface Region Imaging Spectrograph, or IRIS, all lived through that moment. As the spacecraft orbited around Earth, the door of the telescope opened to view the mysterious lowest layers of the sun's atmosphere and the results thus far are nothing short of amazing. The data is crisp and clear, showing unprecedented detail of this little-observed region.
The region of the sun IRIS is observing, the lower atmosphere, and how it powers the sun's scorching upper atmosphere, known as the coronoa, is not well understood. Jay M. Pasachoff, an astronomy professor at Williams College called it "one of the important unsolved problems of astrophysics."
NEXT STORY: This Tiny Blue Dot on Mars Is Our Rover





