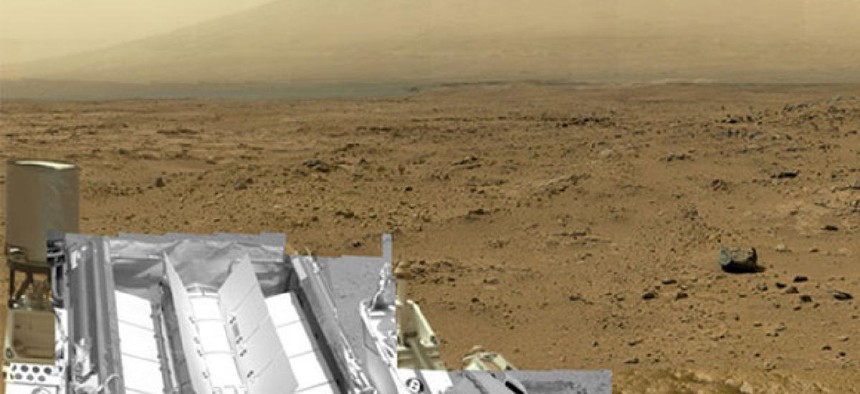
Here You Go, Taxpayers: A Billion-Pixel Image of Mars
NASA
Nearly 1,000 frames, combined into a single Martian mosaic.
The main purpose of the Mars Science Laboratory's mission to the red planet is exactly what its name suggests: science.
There's a secondary mission, too, though, something that has less to do with laboratories and more to do with Mars itself: inspiration. Excitement. Wonder. The simple fact that humans put a roving robot on the surface of a distant planet and can now follow in its footsteps treadmarks from here on Earth.
I mention all that because Curiosity just delivered something new in the wonder department: a 1.3-billion pixel image of the surface of Mars. It's a composite, and zoomable and clickable and interactive. And a little bit addictive.
The individual images, NASA explains, were taken on several different Martian days between October 5 and November 16, 2012. Bob Deen, of the Multi-Mission Image Processing Laboratory at NASA's Jet Propulsion Laboratory, assembled the composite using 850 different frames from the telephoto camera of Curiosity's Mast Camera instrument. He then supplemented those with 21 frames from the Mastcam's wider-angle camera and (and with 25 black-and-white frames -- mostly Curiosity's selfies -- taken from the Navigation Camera).





