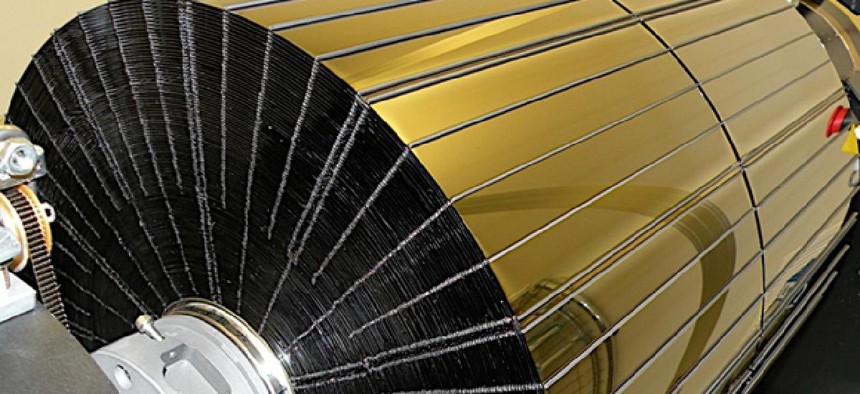
NuSTAR, the latest space telescope, launched
NASA
NuSTAR was launched off the wing of an airplane this week.
For people who remember the X-15 research program from the early 1960s, the launch of a space telescope on Wednesday might have been a bit of deja vu.
Through the X-15 program, NASA, along with the Air Force, the Navy, and North American Aviation conducted research on hypersonic piloted flight, setting an unofficial speed record (4,520 mph) and altitude record (354,200 feet), according to the NASA website . But because the fuel required to reach such speeds and heights was so great, the space agency saved fuel by launching the aircraft from the wings of B-52s flying at 45,000 feet and traveling at 500 mph.
Like the X-15 aircraft, the Nuclear Spectroscopic Telescope Array, or NuSTAR, was launched off the wing of an airplane, in this case an L-1011. And like the X-15, it was launched from a plane in a Pegasus XL rocket to save fuel costs compared with the costs of launching a rocket from the ground, according to NASA.
Once operational in orbit, the telescope "will spend at least two-years observing high-energy X-rays more closely, in higher resolution, than any space telescope before it," NASA said. The X-rays include those emitted by black holes.





