Los Alamos Accused of Disregarding Security During VIP Visits
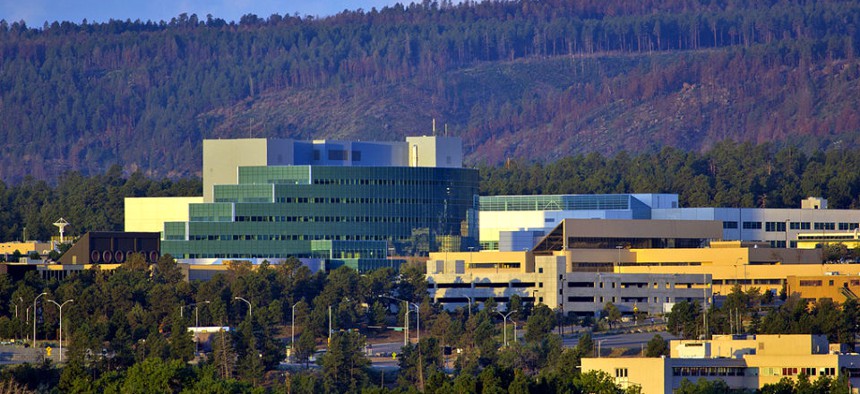
Los Alamos National Laboratory
Whistleblower says he was demoted after reporting the lapse.
A Los Alamos National Laboratory employee with responsibility for site security is charging that the facility suspended some safety procedures during VIP visits in 2011, and then after he complained about the practice retaliated against him because of his outspokenness, the Albuquerque Journal reported.
In a lawsuit filed in federal court Wednesday against the nuclear-weapons laboratory in New Mexico, Michael Irvin alleges he was demoted from his job as a security manager in the LANL director's office after he criticized to his bosses the practice of lifting certain unspecified security practices at the laboratory during spring and summer 2011 visits to the site by important individuals.
Irving's lawsuit asserts he has the right to criticize breaches of laboratory security practices that impact safety around nuclear-weapon materials. His suit claims he has been punished for his whistle-blowing with lost wages and benefits and that he was branded a "troublemaker" and "malcontent" by his manager.
The Los Alamos' public information office did not return the Journal's requests for comment.
The laboratory is home to a number of sensitive nuclear-weapons projects such as the production of plutonium triggers that initiate warhead explosions.
The security practices of the broader U.S. nuclear-weapons complex -- which includes sites in Nevada, Tennessee, New Mexico and California -- has come under heightened scrutiny in the last year following the high-profile summer 2012 break-in by peace activists of a secured area of the Y-12 National Security Complex. Laboratories and other facilities that play a role in maintaining the U.S. nuclear arsenal are overseen by the Energy Department's semiautonomous National Nuclear Security Administration.





