Secret Service mulls bionic ears to detect gunfire at large events
Maria Dryfhout/Shutterstock.com file photo
Camouflaged technology could link to other surveillance systems.
The Secret Service is shopping for camouflaged sensors that can decipher gunshot details amid city hubbub, contracting documents suggest.
The agency, responsible for guarding inaugurations and other U.S. special events, would exercise sole control over the surveillance system, rather than let private analysts send assessments, as many cities are starting to do.
“Due to the secure nature of these sites, a high gunshot detection rate (>95 percent) is strongly desired while daily, operational monitoring of the system by external parties is undesirable,” stated a Jan. 18 survey form for contractors who have products ready to sell.
As prices drop, and geospatial tracking and sound monitoring sharpen, police are embracing gunfire identification technologies. Cities nationwide, including Chicago, Kansas City, Mo., and Palo Alto, Calif., have leased gun detection services online, through the cloud, from security vendor ShotSpotter.
It is unclear whether the Secret Service’s system would be stationed in specific locales or moved for each event.
Agency officials said they want “technologies for fixed site surveillance applications,” covering from “10s to 100s of acres per site, located within urban areas.” But the questionnaire also inquires, “Is the system portable (i.e., can it be quickly relocated to another site)?”
Special event safety increasingly relies on a variety of high-tech monitors, such as city traffic cameras for presidential debates and facial recognition tools for the Super Bowl. Secret Service officials are asking retailers whether their gunfire sensors can be “integrated to communicate with other detection systems.”
A deep data dive on each incident apparently appeals to the agency. Officials want to know whether gunfire reports are able to detail, for instance, the caliber of the weapon, route the bullet took, elevation of the shot and projectile velocity of the ammunition.
One challenge with shot detection is that the location of the shooter – be it hidden inside a car or in a wind tunnel -- can mask blasts. Potential vendors are asked to disclose factors that might impair a system’s perception. And they must address the technology’s ability to parse certain tricky situations such as, multiple shots occurring in a short time interval, from the same or different locations.
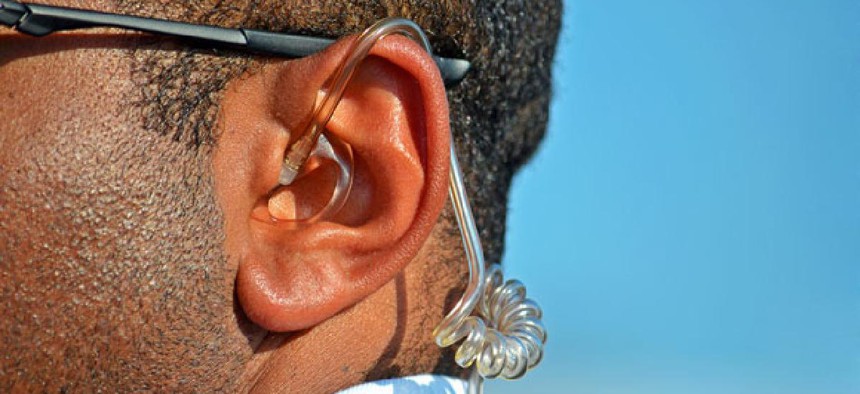
The Secret Service is pursuing technologies that are “easily concealed” or could “aesthetically match their surroundings,” according to the survey sheet.
Shot detectors have sparked privacy concerns because they can pick up ambient noise, like a loud street argument that accompanied a fatal shooting in New Bedford, Mass., according to The New York Times.
ShotSpotter officials told The Times that concerns about privacy are generally unfounded since the detectors “don’t turn on unless they hear a gunshot."
Authorities can obtain critical tips about what to expect upon arriving at a crime scene and potential evidence — such as how fast and in what direction a shooter in a car was traveling, the report added.
NEXT STORY: 2013: The road ahead






