One Chart Shows Why You Shouldn’t Trust the Feds With Your Data

Sergey Nivens/Shutterstock.com
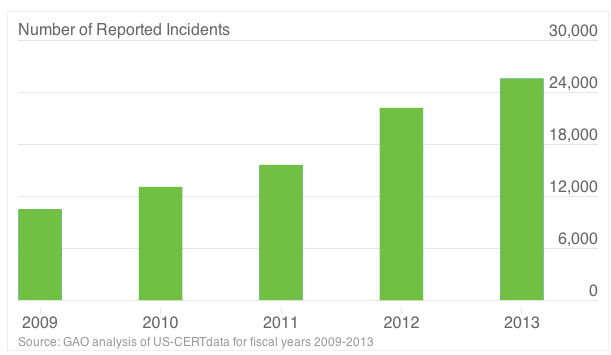
The number of reported information security incidents involving personally identifiable information has more than doubled in recent years.
We reported in January about the spike in government data breaches that has compromised the personal information of federal employees and citizens.
A report released Wednesday by the Government Accountability Office shows that security incidents involving personally identifiable information more than doubled between 2009, when there were 10,481 such breaches, and 2013, when the number climbed to 25,566.
Collectively, the breaches affect hundreds of thousands of people and cost taxpayers millions of dollars. For example, in July 2013, hackers stole a variety of information, including Social Security numbers, bank account numbers and security questions and answers associated with more than 104,000 individuals from an Energy Department computer system. According to Energy’s inspector general, the costs of assisting affected individuals and lost productivity stemming from the breach could top $3.7 million, GAO noted.
Among other problems, GAO noted that only one of seven agencies reviewed by auditors correlated an assigned risk level with breaches of personal information and none of the seven consistently documented lessons learned from their breach responses.