4 Charts That Explain the State of Agency Cybersecurity after the OPM Hack
Most agencies made great strides during the White House-mandated 30-day cybersecurity sprint. But some actually backslid on their use of stronger authentication measures.
Following the massive breach of federal employee files precipitated by a series of cyberintrusions at the Office of Personnel Management, the Obama administration ordered agencies to immediately tighten network defenses during a 30-day “cybersecurity sprint.”
The results are now in. The White House posted details from the cyber review online last week.
Here are a few key takeaways with charts.
First, it’s clear agencies made great strides during the sprint. Across government, agencies increased their use of two-factor authentication.
Overall, the percentage of federal employees required to use a smart card in addition to a password to log on to federal computer networks increased from about 42 percent to more than 72 percent during the cyber sprint, according to new OMB statistics. That’s the single biggest quarterly increase since OMB began tracking the use of two-factor authentication in 2011 when the use of stronger sign-on techniques barely scraped 5 percent.
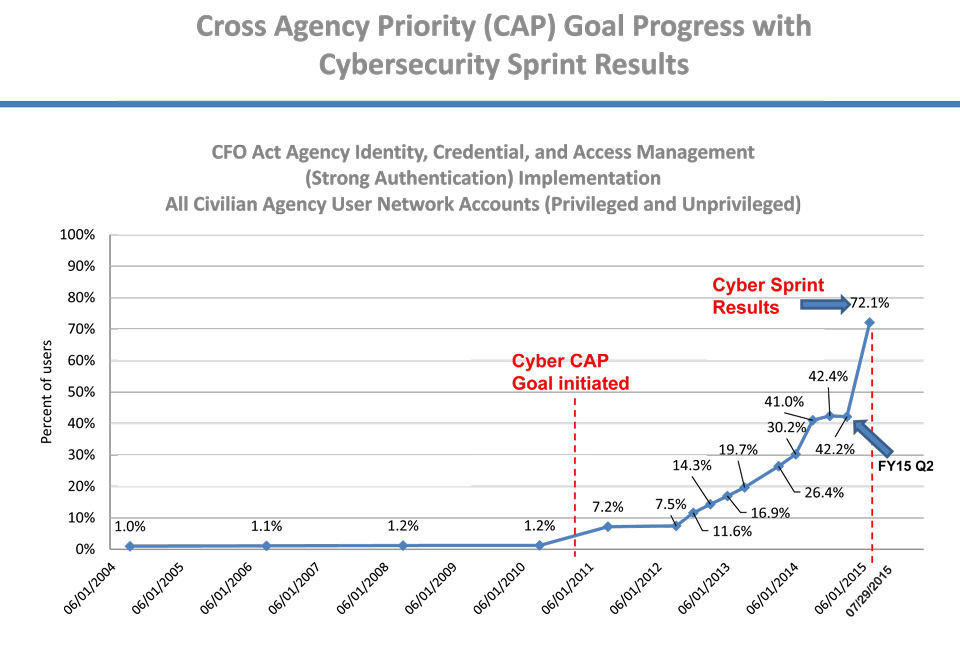
Still, some agencies made only limited progress during the latest cyber push and, somewhat inexplicably, some agencies’ use of two-factor authentication even backslid during the White House’s big cyber push.
The administration’s long-term goal has been to increase the use of two-factor to 75 percent for all users, including those with broad system privileges. After the month-long sprint, 14 agencies made the grade, including OPM and the Interior Department -- both caught up in the recent series of cyberintrusions .
At OPM, the percentage of computers required to use two-factor catapulted from 42 percent before the sprint to 97 percent afterward.
The chart below shows the five agencies with the highest percentage of employees using two-factor sign-ons after the cyber sprint.
Despite the high-profile cyber push by federal Chief Information Officer Tony Scott and the harsh political fallout of the OPM hack -- the agency’s director, Katherine Archuleta; resigned last month -- some agencies continue to lag behind when it comes to implementing stronger sign-ons.
At the agencies below, fell well below the administration’s two-factor targets. At the Energy Department, just 12 percent of users are required to sign on with using two-factor methods.
Somewhat inexplicably, some agencies actually backslid during the cyber sprint when it came to the percentage of employees using strong authentication techniques. Before the big push, for example, 32 percent of Energy employees used two-factor sign-ons. That dropped to 12 percent during the White House-mandated cyber review. The departments of Justice, Education and Defense also reported drops.
Still, some agencies reported massive leaps forward in implementing stronger sign-on measures. The Nuclear Regulatory Commission shot up by nearly 80 percent, for example. Transportation surged from just 32 percent two-factor coverage to 97 percent -- the second highest overall.
( Image via jijomathaidesigners / Shutterstock.com )





