Federal Cybersecurity Spending is Big Bucks. Why Doesn't It Stop Hackers?
Hermin/Shutterstock.com
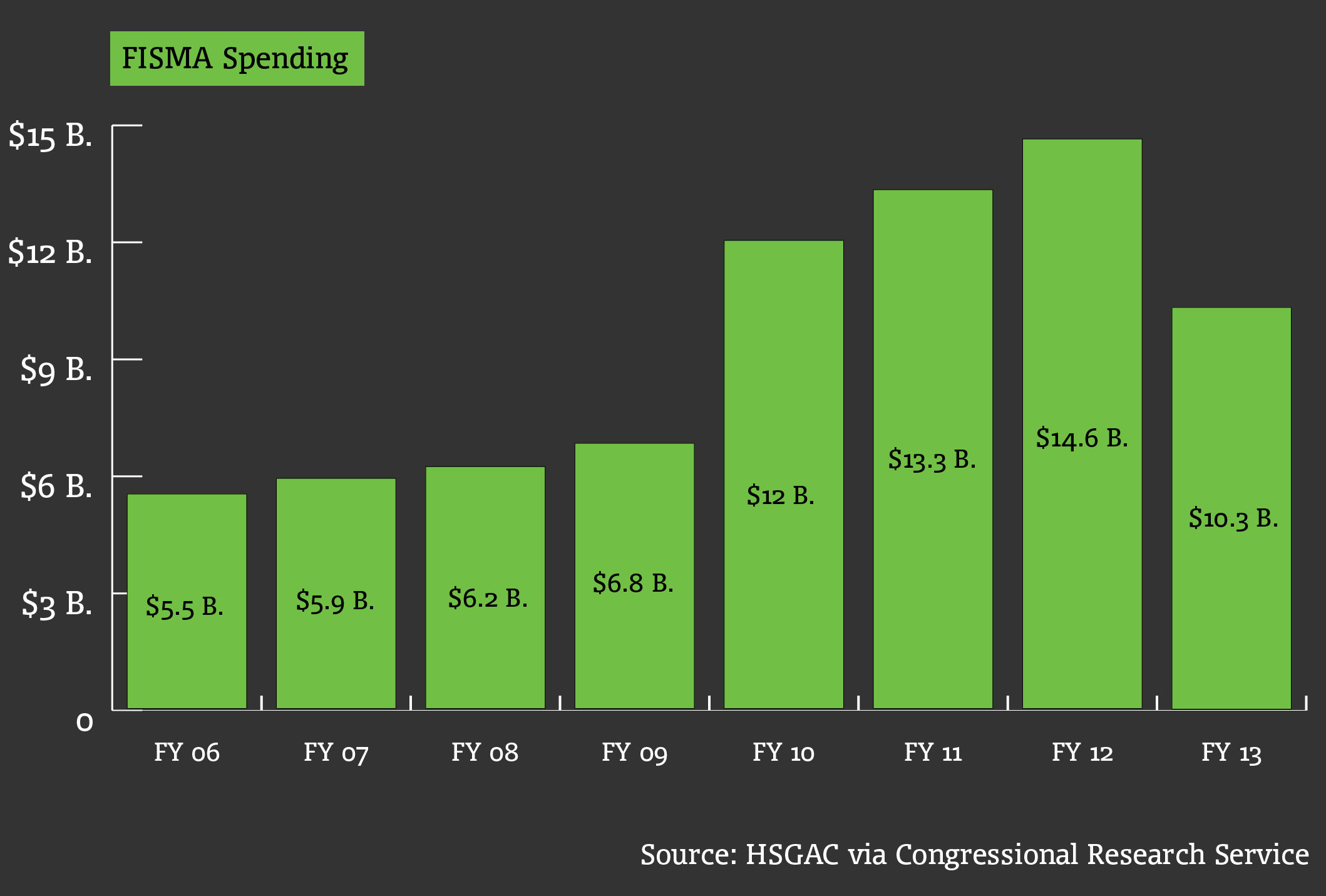
Despite paying $59 billion for data protections since fiscal 2010, the federal government couldn’t stave off hacks against the White House, State Department, Army and dozens of other agencies.
Despite paying $59 billion for data protections since fiscal 2010, the federal government couldn’t stave off hacks against the White House, State Department, Army and dozens of other agencies.
Across-the-board funding cuts last year hit cyber budgets, but the total tab, $10.3 billion, still more than doubles the $4.1 billion industry reportedly spent on computer security. And we all know those corporate expenditures did little to prevent data breaches at Sony, Home Depot and almost every other company, if you count the undetected compromises.
The apparent futility of cyber spending does not bode well for the American population's online security. Government and private systems increasingly are interdependent.
The Pentagon spent $7.1 billion for Cyber Command, the National Security Agency and other military components to defend critical U.S. industry systems at home and abroad. Nevertheless, banks, along with airports, were hacked.
The largest U.S. financial institution, JPMorgan, spent $250 million on cybersecurity, only to have attackers pry open records on 83 million households and small businesses.
In an exit report by former Sen. Tom Coburn, R-Okla., who left Congress Monday, the avowed penny pincher said "federal information security remains a significant challenge for an overwhelming majority of federal civilian agencies” despite billion-dollar investments.
The Homeland Security and Governmental Affairs Committee, where he served as top Republican last Congress, provided Nextgov with a Congressional Research Service memo that breaks down annual spending on cybersecurity compliance, under the Federal Information Security Management Act.
Now, though, even some privacy hawks say it might be time for everyone to stop pouring money into system controls and use government-operated network monitoring technology.
"The big banks, big retailers and big media companies whose hacks make the front pages are not being penetrated because they've skimped on security out of sloth, stupidity or greed," Alan Raul, former vice chairman of the White House Privacy and Civil Liberties Oversight Board, said Monday in a Wall Street Journal op-ed.
There is not much businesses could have done to prevent some of these intrusions, "any more so, in fact, than the White House, Air Force, Postal Service, Commerce and State Departments, [Federal Trade Commission], or countless other federal hacking victims, could guarantee their own cybersecurity,” added Raul, now head of Sidley Austin's privacy, data security and information law practice.
One proposal would have the government offer companies an automated cyberdefense system, called EINSTEIN, that detects and deflects hackers. Internet service providers for the government have long used the technology to collect information on potential agency compromises, and last month it became capable of redirecting bad guys away from government employee computers.
"If EINSTEIN is in fact working, the government should make it available more broadly," said Raul, stressing that the government would then have to broaden the authority of federal civil liberties bodies.
In the wake of the Sony attack, Rep. Dutch Ruppersberger, D-Md., on Friday is expected to reintroduce controversial legislation that would facilitate an EINSTEIN-like system for industry, The Hill reports. The Cyber Intelligence Sharing and Protection Act, better known as CISPA, would exchange details about malicious activity collected by companies and the government so all parties can tweak their antivirus programs accordingly.
Could letting Big Brother see certain network activity, under strict privacy protocols, save some big bucks?
(Image via Hermin/Shutterstock.com)






