Feds: NSA ‘Probably’ Spies on Members of Congress
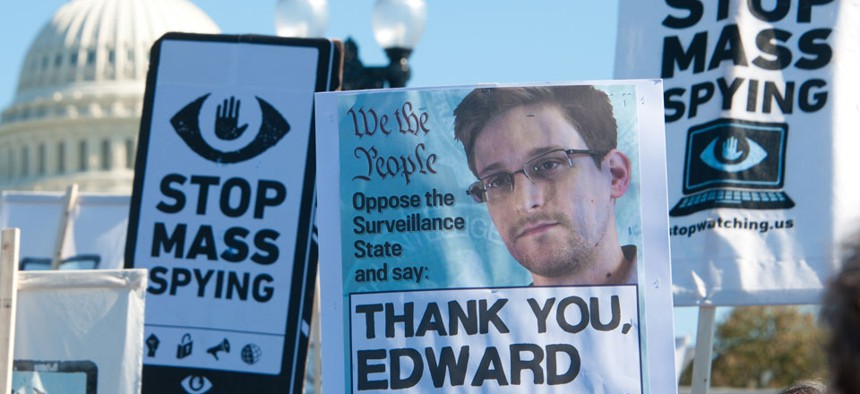
Rena Schild/Shutterstock.com
The admission is hardly surprising, but expect lawmakers to feign outrage anyway.
The National Security Agency "probably" collects phone records of members of Congress and their staffs, a senior Justice Department official conceded Tuesday.
Deputy Attorney General James Cole buckled under questioning from multiple lawmakers during a House Judiciary Committee hearing reviewing proposals to reform the NSA's surveillance activity.
Rep. Zoe Lofgren, a California Democrat, began by asking Peter Swire, a member of the president's handpicked surveillance review board, whether lawmakers' numbers are included in the agency's phone-records sweeps. Swire protested that he was not a government official and couldn't best answer the question, but said he was unaware of any mechanism that "scrubbed out" member phone numbers from the agency's data haul.
Lofgren's time expired and Rep. Darrell Issa, a California Republican, then put the question to Cole.
"Mr. Cole, do you collect 202-225 and four digits afterwards?" Issa asked, referring to the number code used to call congressional offices.
"We probably do, Mr. Congressman," Cole responded. "But we're not allowed to look at any of those, however, unless we have reasonable, articulable suspicion that those numbers are related to a known terrorist threat."
While the admission is hardly surprising, given that the raison d'être of the NSA's sweeps is to collect data of virtually all Americans, it may mark the first time the government has responded so directly to the question.
Several members of Congress have recently agitated to know whether their phone records are included in the NSA's sweeping data grabs. Last month, Sen. Bernie Sanders, a Vermont independent, sent a letter to NSA Director Keith Alexander asking whether Congress was spied on.
In response, Alexander said that "nothing NSA does can be fairly characterized as 'spying on Members of Congress or other American elected officials.' " His letter did not explicitly say whether congressional phone records were gathered, however.
(Image via Rena Schild / Shutterstock.com)






