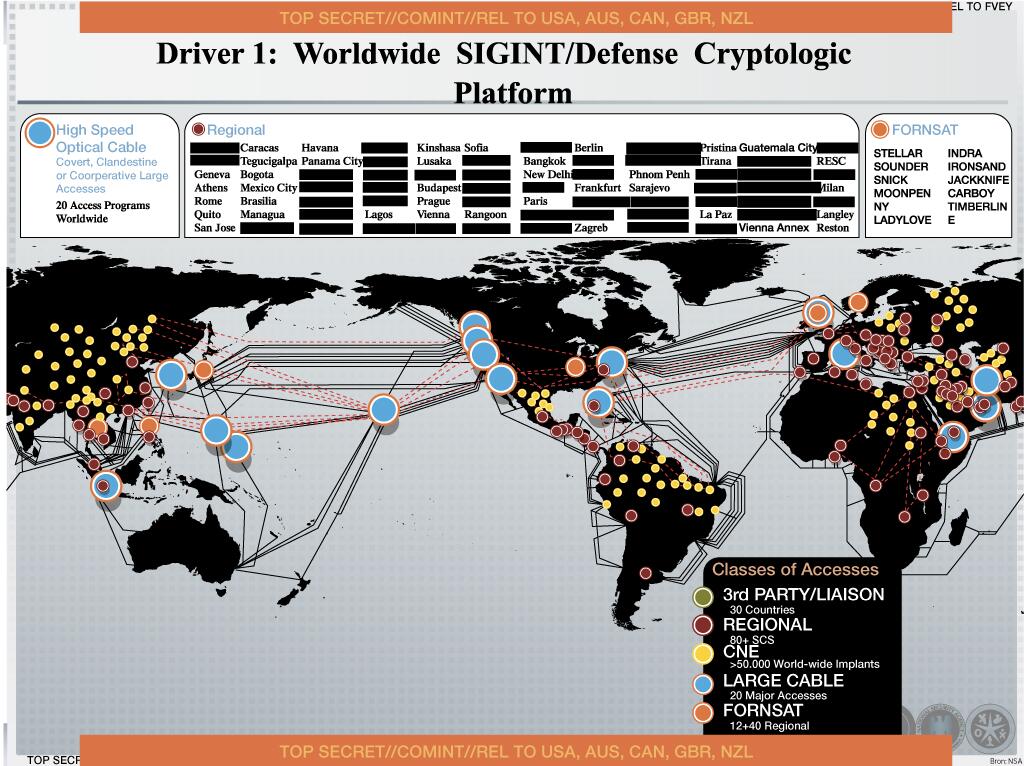
Map Shows the NSA's Massive Worldwide Malware Operations

Finchen/Shutterstock.com
NSA hackers have reached companies across the world.
A new map details how many companies across the world have been infected by malware by the National Security Agency's team of hackers, and where the companies are located.
Dutch newspaper NRC Handelsblad reports the NSA uses malware to infect, infiltrate and steal information from over 50,000 computer networks around the globe. This new, previously unreported scope of the NSA's hacking operation comes from another PowerPoint slide showing a detailed map of every infection leaked by former contractor Edward Snowden.
The British intelligence service liked this strategy too, NRC Handelsblad reports, because they successfully duped a Belgium telecom company with a fake LinkedIn account. A strip at the bottom says the map is relative to relative to the U.K., Australia, New Zealand, and Canada, the "Five Eyes" nations that share intelligence.
Read the full story at TheWire.com.
(Image via Finchen/Shutterstock.com)