Federal computer security grade improves slightly in '07
But some say the report card’s finding means little in light of its shortcomings.
Comment on this article in the Forum Read the related blog entry
Agencies reported a nominal improvement in computer security in fiscal 2007, according to an annual report card, but industry analysts still assert the grades should never have been issued because recent congressional hearings have shown them to be meaningless.
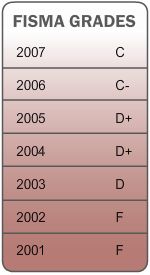
Overall, the government received a grade of C for how well it has complied with the Federal Information Security Management Act, which Congress passed in 2002 to improve the security of federal networks. The grade was the highest government has received so far, although it was only a slight increase from the C minus it earned in fiscal 2006, according to the report card released by Rep. Tom Davis, R-Va.
The report card rated agencies on annual tests of information security, plans of action and milestones or corrective-action plans, certification and accreditation of systems, management of the computer security configurations, detection and response to breaches, training programs, and the accuracy of their inventories.
The biggest improvement came from the Homeland Security Department, which jumped from a D in fiscal 2006 to a B in fiscal 2007. Congress heavily criticized DHS last year for poor information security practices.
"We have made impressive progress on securing our computers and networks since the department stood up, and we have taken great strides to institutionalize rigorous network security and data and privacy protection programs," said DHS spokesman Larry Orluskie. "Our goal in 2007 was to raise the bar to improve baseline for controls, and we met that goal. We are continuing in 2008 to build a robust enterprise security operations program."
The Energy Department also saw moderate improvement, rising to B plus from a C minus.
In contrast, the Labor and Transportation departments saw the most significant drops in computer security. Labor fell from a B minus to an F, and Transportation dropped from a B to an F. In all, eight agencies received an F in 2007 compared with nine in 2006. The Veterans Affairs Department, which received an F in 2006, received no grade because it had not completed its FISMA reports in time.
But some say the grades mean little, given that they're derived from annual reports on how well agencies have complied with FISMA, which measures compliance with security processes rather than the effectiveness of security measures an agency may or may not have taken.
"Whoever advised Tom Davis that he should release the score card now -- after House and Senate testimony that the FISMA scores do not measure security -- should be fired," said Alan Paller, director of research at the SANS Institute, a nonprofit cybersecurity research organization in Bethesda, Md., and a longtime critic of FISMA.
In February, Congress expressed concern about FISMA's reliance on certification and accreditation of systems, rather than on testing how vulnerable government networks actually were.
In addition, Rep. Jim Langevin, D-R.I., in May introduced the 2008 Homeland Security Network Defense and Accountability Act (H.R. 5983), which requires DHS to test whether systems are compliant with security protocols and to assess its ability to defend against known cyberattacks networks that the department operates and those maintained by contractors.
"This is an example for the textbooks," Paller said. "First, Congress creates waste by writing FISMA in a way that demands useless reporting, and then it highlights the useless scores in a way that in some cases provides incentives for federal agencies to deliver misleading results."





