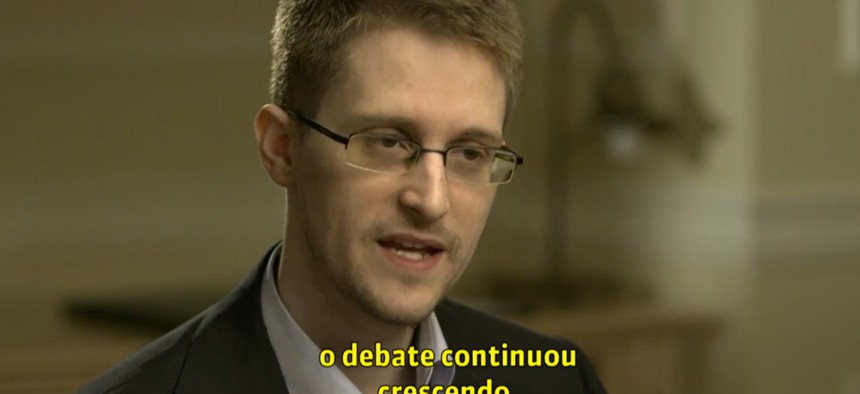
Edward Snowden: I Had More Access Than Almost Any Other Official in the Intelligence Community
Globo.com
The man responsible for leaking classified National Security Agency documents says he wasn't just "some low-level employee."
Almost a year after Edward Snowden revealed himself as the man who blew the whistle on the National Security Agency, some people are still wondering how he had access to so many classified intelligence documents.
After all, Snowden was young. He was just a contractor. "How did a 29-year-old have access to all those classified documents?" asked Sonia Brindi of the Portuguese television network Globo during a lengthy new interview with Snowden in Moscow. (Watch it in full here). "How did you access them?"
The public's bewilderment is misplaced, Snowden replied. "There's sort of been a misinformation occurring in the U.S. media, that was then propagated by the international media, which was that I was some low-level employee, I didn't really have any understanding of these materials," he said. "I had functioning at a very senior level. I've written policies on behalf of the United States. I had been in meetings with the very top technical officials on the NSA and the CIA."
Snowden had more responsibility at the NSA than people may think, he said. "I was what's called a systems administrator or a superuser, which means that I had more access than almost any other official in the intelligence community," he said. "Because even the director of the National Security Agency or the Central Intelligence Agency or any of these things, when they want to see some documents, when they want to understand some program, they have to ask someone: 'Show me this, tell me about this, brief this for me.' "
And that someone was Snowden. "As a systems administrator, you are the person who can see all of that, because you are the one who controls all of the information."
Snowden's latest interview comes two days before the one-year anniversary of the first NSAleak, which showed that the agency collects phone records of millions of Verizon customers every day. Back then, Snowden told Globo he wanted to stay out of the spotlight. Now, things are different. "I'm confident that today, now nearly a year on from the initial revelations, I can talk about things. I can talk about how I feel and it's not going to take away from the debate."
Returning to the U.S., however, is still not an option. "I would love to face court in the U.S.," he said—but only if reforms are made to the Espionage Act, the legislation under which Snowden has been charged with three felonies for leaking information.






