DISA returns to the drawing board on cloud plans
Pentagon CIO must evaluate commercial cloud services before funding the agency to host military applications online.
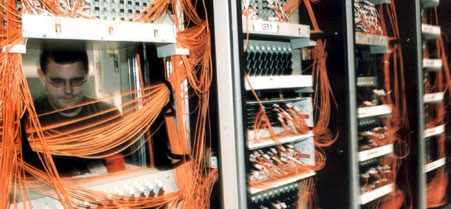 Congress told Defense to switch to private services, such as this Silicon Valley server farm, offering the same security at a lower cost.
Congress told Defense to switch to private services, such as this Silicon Valley server farm, offering the same security at a lower cost.
The Pentagon has pushed back a Jan. 15 deadline for military services and federal agencies to report on congressionally mandated strategies for downsizing computer rooms, a Defense Information Systems Agency official said. A provision in the 2012 National Defense Authorization Act , enacted two weeks ago, had ordered Defense Department components to develop plans by that date as part of a recommended Defensewide shift to commercial cloud services.
The mandatory rethinking could upend ongoing efforts to save $680 million annually by providing information technology services through DISA clouds.
Defense Department Chief Information Officer Teri Takai intends to instruct military agencies on how to comply with Congress' request within the next few weeks, Tony Montemarano, DISA director for strategic planning and information, told Nextgov . The legislation requires Takai by April 1 to submit to Congress a departmentwide approach for reducing the equipment, utilities and personnel supporting military server farms.
Congress directed the Pentagon to switch to private cloud services that offer the same degree of security at a lower cost as DISA-operated computer services. During remarks at a Tuesday conference hosted by the Armed Forces Communications and Electronics Association, however, Montemarano noted that the law means Defense must "look at how it's going to move cloud computing to a commercial environment -- to the degree it can." That qualification means the military must first study whether private data centers are even capable of meeting the department's safety and price requirements, he said.
The law already has delayed the Army's migration of unclassified email to a cloud operated by DISA. Until the service submits a cost-benefit analysis and categorizes the endeavor as a formal acquisition program overseen by the Army's acquisition executive, military officials cannot use congressional funds for the transition.
"I think they have done due diligence, but Congress has asked for some formality," Montemarano said. "I'm sure we'll be off and running within a month or two."
To better coordinate Defensewide IT consolidation, DISA on Tuesday created a single enterprise services division that officially will launch mid-February, said Alfred Rivera, DISA director for computing services.
NEXT STORY: Former federal CIO Vivek Kundra joins industry






