Why We Can't Name a Planet After Joe Biden—Yet
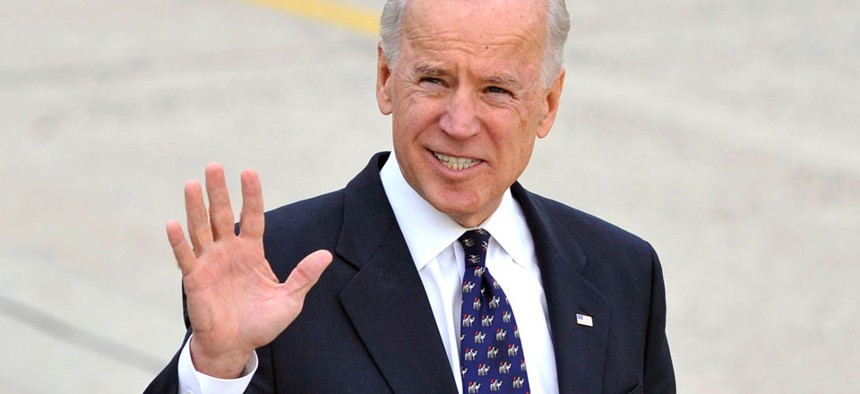
Defense Department file photo
Astronomers have discovered a new dwarf planet. For now, they're calling it 'Biden.'
Astronomers have discovered a possible new dwarf planet: a cold, relatively tiny lump of ice traveling near the barrier where the sun loses all its gravitational influence.
The planet—280 miles in diameter—is roughly the size of Wisconsin. And despite the planet's relative smallness, this discovery has ignited astronomers' excitement: Its existence and orbit may be able to tell us about the origins of the solar system.
But never mind all that. More importantly, the scientists gave the planet a nickname, and that name is "Biden."
"The newfound object's official name is 2012 VP113, but the discovery team calls it VP for short, or just 'Biden,' " the journal Nature, which published the findings, reports.
It will be some time before the dwarf planet gets an official name. The International Astronomical Union needs iron-clad evidence that the celestial body does in fact exist and adheres to the definition of a dwarf planet.
But when it comes down to deciding, the planet's name will not be Biden.
It won't be for any fault in the vice president. Rather, according to the IAU, "names for persons or events known primarily for their military or political activities are acceptable only after 100 years elapsed since the person died or the event occurred."
So there will be no Dwarf Planet Biden, Bush, Clinton, or Obama until the next century.
The IAU's other planet-naming rules are wonderfully nerdy, and worth reading through. Those who find the planet are allowed to suggest a name, but the names are officially selected by a 15-judge committee.
Generally, the heavens employ a Roman theme. But in some circumstances, the rules are highly specific. For example (emphasis mine):
• "Objects in orbits between the orbits of Jupiter and Neptune, and not in 1:1 resonance with any major planet, are to receive names of centaurs."
• "Objects in orbits in 3:2 resonance with Neptune are to receive names of underworld deities."
• "Names of pet animals are discouraged."
• "Names of a purely or principally commercial nature are not allowed."
So no planet Verizon, either.






