Congress Cracks Down on Purchases of Chinese-Made IT
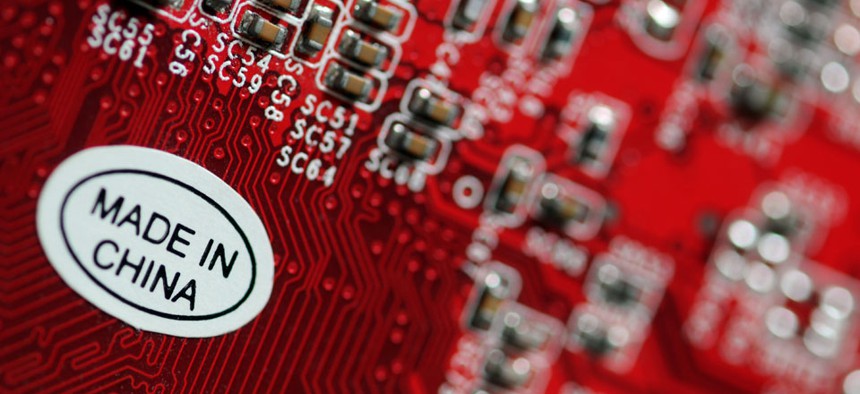
Arkadiusz Komski/Shutterstock.com
Spending bill bars NASA, Commerce, Justice, and NSF from buying systems from China until vetted by authorities and restricts supercomputer acquisitions.
Legislation expected to pass both the House and Senate by late this week bars several departments from buying Chinese-manufactured computer equipment until federal authorities conduct special inspections. The stipulation faces opposition from some unlikely corners though: U.S. businesses allegedly hacked by China have said the move will probably slow acquisitions and hurt American multinational companies.
The provision, included in a fiscal 2014 spending package up for a House vote today, is a reaction to China's alleged gross theft of U.S. trade secrets and classified intelligence. Lawmakers folded a similar policy into fiscal 2013 funding legislation.
The measure directs the departments of Commerce and Justice, NASA and the National Science Foundation to screen for “any risk of cyber-espionage or sabotage” in computer systems "produced, manufactured, or assembled" by entities "that may be owned, directed, or subsidized by the People’s Republic of China."
Last spring, industry associations argued that discrimination against China could encourage retaliation, and the mandatory audits could delay installation of new federal security systems.
"The requirement to assess every IT product purchase, absent any triggering threshold, will likely slow the federal acquisition process and put impacted federal agencies behind the security innovation curve because they would not be acquiring and using the latest security innovations," the technology organizations wrote in a letter to lawmakers. Cosigners included the Chamber of Commerce, whose own data reportedly was compromised by Chinese hackers in 2011.
Another somewhat protectionist stipulation in the 2014 measure essentially outlaws military supercomputers developed anywhere outside the United States. The Pentagon cannot purchase a foreign-built machine without certifying to Congress that capable U.S.-made systems are not available, according to the legislation.
A recently-enacted defense authorization bill directs the Energy Department to create “exascale” supercomputers for simulating nuclear weapons explosions. The machines would run at a speed of a quintillion operations per second. That is 1,000 times faster than the pace of the present record holder, a supercomputer developed by China’s National University of Defense Technology that can perform 34 quadrillion calculations per second.
(Image via Arkadiusz Komski/Shutterstock.com)





