GSA’s Crowdsourcing Website Named Finalist for Innovation Award
Multi-agency distressed neighborhood initiative also highlighted among 600 applicants.
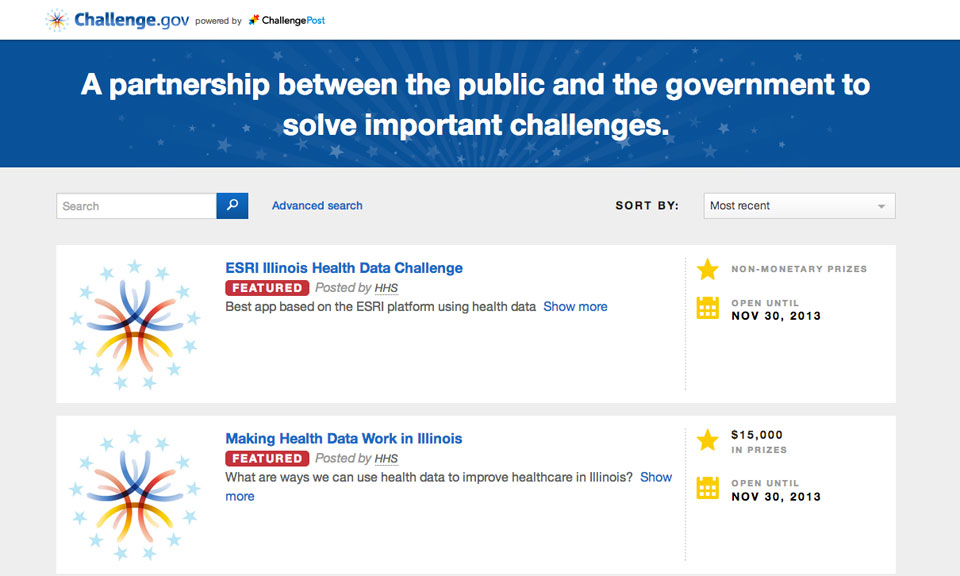
Challenge.gov, the General Services Administration’s online portal for crowdsourcing solutions to agency problems, is among five finalists for the prestigious Innovations in American Government Award sponsored by the Ash Center for Democratic Governance and Innovation at Harvard University’s Kennedy School.
The Ash Center -- named for Roy Ash, the first director of the Office of Management and Budget created under the Nixon administration, and his wife Lila -- announced on Tuesday that GSA’s site was among five finalists for the annual contest highlighting successful programs in city, county, state and federal government. Finalists were selected from among 600 applications.
Also named a finalist is a multiagency federal program to address the interconnected problems of distressed neighborhoods. The program involves the Education, Justice, Health and Human Services, Housing and Urban Development, and Treasury departments.
The winner of the award, which is funded by the Ford Foundation and intended to highlight programs for replication by other agencies, will be announced in December.
GSA’s Challenge.gov site allows the government to crowdsource solutions to problems in a contest format, “bringing diversity in solutions and contributors,” said the center in a statement. “This is a pay-for performance model that saves money on key initiatives and broadly drives innovation within and beyond government.”
The news was welcomed in a Tuesday blogpost by GSA’s Kelly Olson, director of strategic initiatives at the agency’s Office of Citizen Services and Innovative Technologies. Since Challenge.gov was launched in September 2010, she noted, it has hosted more than 300 crowdsourcing competitions in which some 60 federal agencies have awarded more than 200 prizes. “It now averages six new challenge and prize competitions a month,” Olson said. “Agencies are increasingly turning to Challenge.gov to conduct software and apps challenges, to meet the vision of a more citizen-centric digital government."
The other finalists for the Ash award are King County, Wash., for savings in employee health care; the city of Boston’s Office of New Urban Mechanics for its enhanced citizen services; and the State of New Mexico’s “smart” truck inspection system that identifies high-risk targets while minimizing disruptions to traffic.