Timeline: Bold Ideas Well Applied Can Change the World
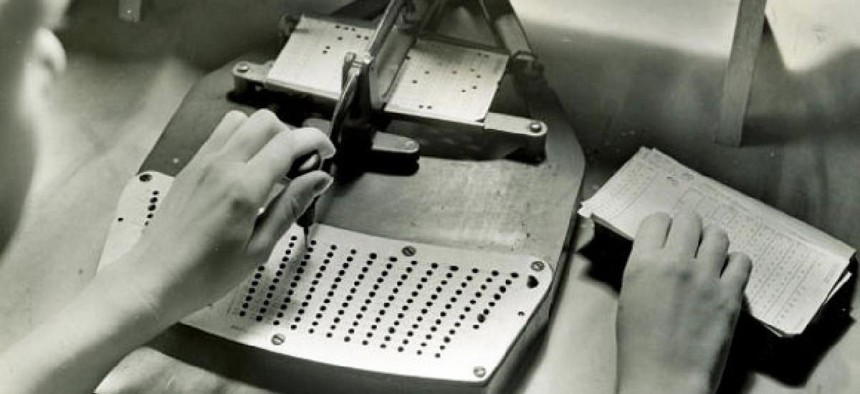
The tabulator revolutionized accounting. U.S. Census Bureau
From the transcontinental telegraph to the Human Genome Project, federal agencies have spurred some of the nation’s greatest breakthroughs.
What does the Interstate Highway System have in common with the Human Genome Project? More than one might think. They both were ambitious programs that changed the world. In the digital age, the network of roads funded by the Eisenhower administration may not seem like a world-changing endeavor. But by some calculations, it was the largest public works project since the Egyptian pyramids, and it provided the framework for America’s then-emerging superpower status. The DNA sequencing project promises to revolutionize medicine and our understanding of human development. What’s more, both programs were federally funded and conceived.
In this time of furloughs and fed-bashing, it’s easy to forget how powerful a good idea smartly implemented can be. A recent survey of federal employees found that fewer than 40 percent believe they work in a culture of innovation. That’s a shame, because government innovation and investment in promising technologies have fueled some of the nation’s most transformative initiatives.
We pulled together a few examples of how public investment of treasure -- and, in some cases, blood -- spurred great advancements. This is not an exhaustive list, of course, but it hints at the breadth and depth of the nation’s debt to the men and women who aren’t afraid to think boldly and act smartly to improve the world around them.
Kedar Pavgi contributed to this report.





