Bill to increase oversight of IT projects gets big boost from report
GAO finds $3 billion in cost overruns for IT projects, adding support for a Senate proposal requiring agencies to post reasons for cost overruns on major projects.
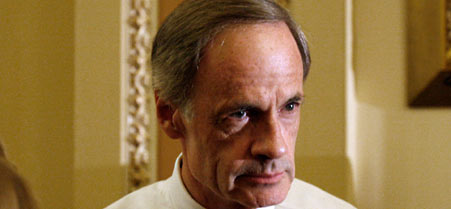 Sen. Tom Carper requested GAO write the report.
Sen. Tom Carper requested GAO write the report.
A report released on Friday that forecasts $3 billion in cost overruns on 16 major projects has pushed lawmakers to move forward on a bill designed to tighten oversight of federal information technology programs.
The Government Accountability Office report examined how the eight civilian agencies that account for the most spending on information technology measured how their IT investments varied from the original costs and schedules -- a process known as earned value management. Every one of the agencies had major problems in determining earned value management, said Dave Powner, director of IT management issues at GAO and author of the report . As a result, the agencies were unable to accurately identify the progress contractors had made on IT projects.
"Earned value management is a proven management technique that we really want to enforce, especially with large projects that have a track record of failure," Powner said. GAO looked at some of the largest projects in the federal government to develop a sense for how agencies were implementing earned value management, he said.
The 16 projects exceeded their original cost estimates by $2 billion, with most of that coming from four projects: two Census Bureau contracts for handheld computers and a computer system to support the 2010 census, the Homeland Security Department's trade system , and NASA's Mars Science Laboratory.
GAO projected additional cost overruns totaling $1 billion for the 16 projects, although two of them accounted for more than 80 percent of that figure: NASA's James Webb Space telescope and the Veteran's Affairs health IT modernization program.
"The report says the projects were already $2 billion over budget collectively, so it wasn't like they didn't have a troubled past," Powner said. "If the project's past is troubled, you really should be staying on top going forward. You can reverse the trends if you jump in there and address root causes. There's a possibility the additional billion doesn't have to be if you get in there and reverse those trends."
GAO's findings are expected to elevate the profile of the 2009 Information Technology Oversight and Waste Prevention Act, a bill introduced in April by Sen. Tom Carper, D-Del., that would increase the oversight of IT investments, a Senate staffer told Nextgov. Carper, chairman of the Federal Financial Management Subcommittee, requested GAO write the report.
The full Senate is expected to vote on the bill within the next month. The bill was voted out of committee in May, and the committee report is expected to be released next week. It has attracted bipartisan support and has been endorsed by industry groups TechAmerica and the Professional Services Council as well as federal chief information officer Vivek Kundra.
One of the bill's provisions calls for the creation of a Web site that would publish information on the status of federal IT investments, similar to the Federal IT Dashboard , which Kundra launched this year. Powner praised the dashboard but said the data is unreliable. The bill would build upon the dashboard, but require the data be more accurate and the information be published not only on which projects are over-budget and by how much, but also the reasons why they are over budget.
"The goal of our bill is not to harass agencies with excessive reporting and oversight," Carper said. "But Congress needs more information about these projects so we can decide whether we want to continue funding them or not."
Carper and Sen. Susan Collins, R-Maine, released a statement calling the overruns unacceptable and indicative of the larger state of IT management in the federal government. "At a time when our country faces record deficits and dramatic budget cuts, it is unacceptable that agencies are not telling Congress and the taxpayers the true costs for these large-scale technology investments," they said. "And, because the GAO looked at only 16 of the many federal IT projects needed to protect our country, it seems we could really be looking at many more billions of dollars of cost overruns on technology that will be delivered obsolete and broken."
NEXT STORY: Anti-Social Feds





