McCain suggests using military tech on Mexico border
The Arizona senator describes drug cartels' operations in the area as irregular warfare and says the rising violence justifies a military response, including the use of technology such as unmanned aerial vehicles.
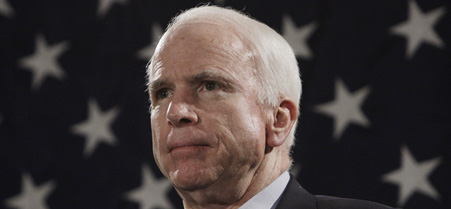 Sen. John McCain says he is more concerned about the security of the border than he has ever been.
Sen. John McCain says he is more concerned about the security of the border than he has ever been.
Sen. John McCain, R-Ariz., said on Thursday the operations of drug cartels along the U.S.-Mexico border are tantamount to war and urged a top military commander to deploy high-tech military systems to monitor activities in the area.
"I can make an argument that we are [engaged] in combat on the border," McCain said during a hearing of the Senate Armed Services Committee, which was considering the nomination of Vice Adm. James "Sandy" Winnefeld Jr. to head U.S. Northern Command. He called the $65 billion-per-year drug trade in that region, which has resulted in murders on both sides of the border, a "corrosive effect" on life in the Southwest.
McCain has represented Arizona, which shares a 1,400 mile border with Mexico, in the House and Senate since 1982. The senator said he was more concerned about the security of the border than he has ever been, given what he described as irregular warfare operations by drug cartels.
A 58-year-old rancher in southeast Arizona was found shot to death on March 27. Investigators speculated that he was killed by a drug smuggler who had illegally crossed the border.
McCain told Winnefeld the violence justifies a military response, including sending the kind of advanced systems the Defense Department is using in Iraq and Afghanistan to the Mexico border.
U.S. Northern Command, established in 2002 and headquartered at Peterson Air Force Base in Colorado Springs, Colo., is responsible for homeland defense. "We have an obligation to protect our borders," McCain said, adding he would like to see military surveillance systems, including unmanned aerial vehicles, used in the region.
Winnefeld said he shared McCain's "deep concerns over the level of violence on the border" and would make a trip to the area with the senator one his first priorities when taking over the command. Winnefeld did not address McCain's request to use the military's computer systems.
NEXT STORY: What Meaningful Use Can Do






